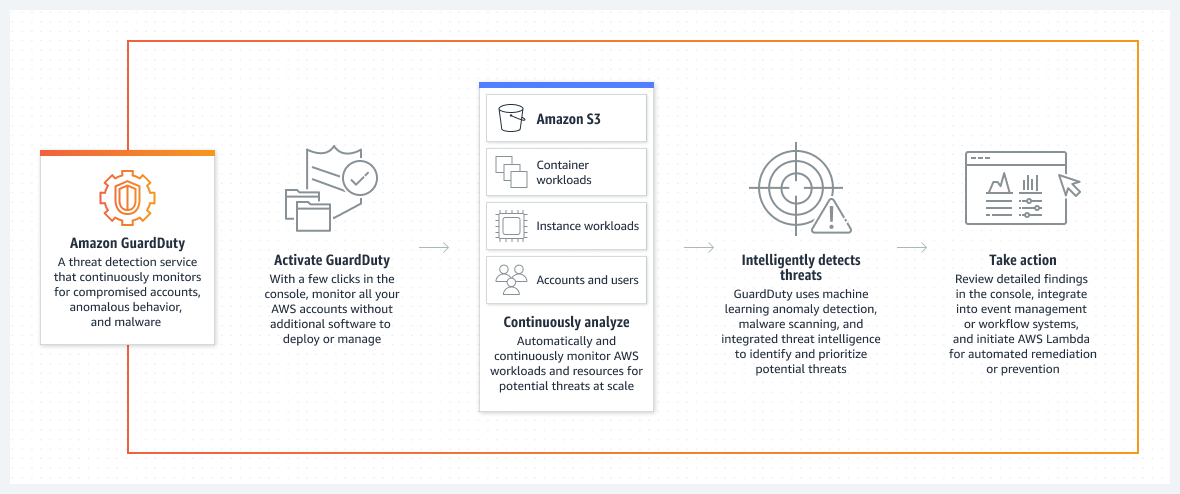
Amazon GuardDuty
- Amazon GuardDuty is a threat detection service that continuously monitors the AWS accounts and workloads for malicious activity and delivers detailed security findings for visibility and remediation.
- is a continuous security monitoring service that analyzes and processes the following data sources:
- CloudTrail S3 data events and management event logs,
- DNS logs,
- EKS audit logs, and
- VPC flow logs.
- uses threat intelligence feeds, such as lists of malicious IP addresses and domains, and machine learning to identify unexpected and potentially unauthorized and malicious activity within the AWS environment.
- combines machine learning, anomaly detection, network monitoring, and malicious file discovery, utilizing both AWS-developed and industry-leading third-party sources to help protect workloads and data on AWS
- is a Regional service and is recommended to be enabled in all supported AWS Regions. This helps generate findings of unauthorized or unusual activity even in Regions not actively used.
- does not look at historical data, it monitors only the activity that starts after it is enabled.
- operates completely independent of the AWS resources and therefore has no impact on the performance or availability of the accounts or workloads.
- GuardDuty supports
- Suppression rules, allow the creation of very specific combinations of attributes to suppress findings.
- Trusted IP List for highly secure communication with the AWS environment. Findings are not generated based on trusted IP lists.
- Threat List for known malicious IP addresses. Findings are generated based on threat lists.
- Security findings are retained and made available through the GuardDuty console and APIs for 90 days, after which they are discarded.
- Findings are assigned a severity, and actions can be automated by integrating with Security Hub, EventBridge, Lambda, and Step Functions.
- Amazon Detective is also tightly integrated with GuardDuty which helps perform deeper forensic and root cause investigations.
- GuardDuty Malware Protection feature helps to detect malicious files on EBS volumes attached to an EC2 instance and container workloads.
GuardDuty with Multiple Accounts
- GuardDuty has multi-account management through AWS Organizations integration, which allows delegating an administrator account for the organization.
- The delegated administrator (DA) account is a centralized account that consolidates all findings and can configure all member accounts.
- The administrator account helps to associate and manage multiple AWS accounts.
- All security findings are aggregated to the administrator account for review and remediation.
- CloudWatch Events are also aggregated to the administrator account when using this configuration.
GuardDuty Automated Remediation
- GuardDuty security findings can be remediated automatically using EventBridge and AWS Lambda
- For example, a Lambda function can be created to modify the AWS security group rules based on security findings. For a GuardDuty finding indicating one of your EC2 instances is being probed by a known malicious IP, the address can be added through an EventBridge rule, initiating a Lambda function to automatically modify the security group rules and restrict access on that port.
GuardDuty Malware Protection
- GuardDuty Malware Protection helps scan EBS volume data for possible malware and identifies suspicious behavior indicative of malicious software in EC2 instances or container workloads.
- is optimized to consume large data volumes for near real-time processing of security detections.
- scans a replica EBS volume that GuardDuty generates based on the snapshot of the EBS volume for trojans, worms, crypto miners, rootkits, bots, and more.
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- Which AWS service makes detecting and reporting unexpected and potentially malicious activity in your AWS environment easy?
- AWS Shield
- AWS Inspector
- AWS GuardDuty
- AWS WAF