Table of Contents
hide
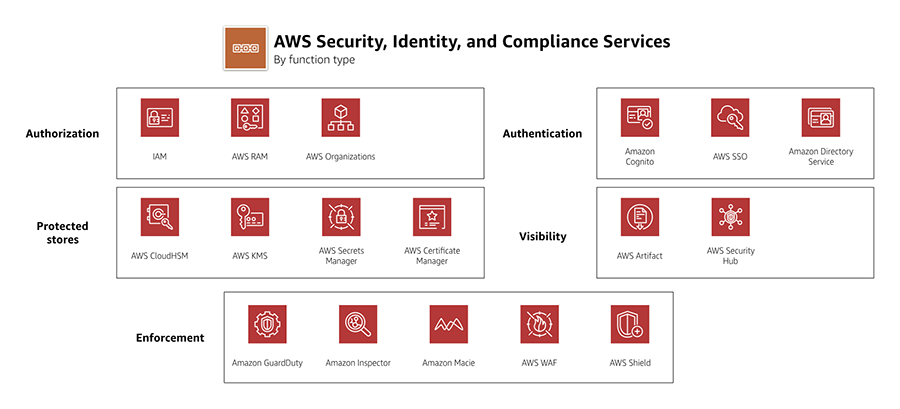
AWS Security Services Cheat Sheet
AWS IAM Identity Center (Successor to AWS SSO)
- is a centralized workforce identity management service that provides single sign-on (SSO) access to multiple AWS accounts and business applications.
- was renamed from AWS Single Sign-On (AWS SSO) in July 2022.
- enables administrators to define, customize, and assign fine-grained access across AWS accounts and applications.
- provides workforce users a portal to access AWS accounts and cloud applications assigned to them.
- supports integration with external identity providers (IdPs) like Microsoft Active Directory, Okta, and Azure AD.
- simplifies multi-account access management through AWS Organizations integration.
- provides temporary credentials instead of long-term IAM user credentials.
- supports attribute-based access control (ABAC) for fine-grained permissions.
Key Management Service – KMS
- is a managed encryption service that allows the creation and control of encryption keys to enable data encryption.
- provides a highly available key storage, management, and auditing solution to encrypt the data across AWS services & within applications.
- uses hardware security modules (HSMs) that are FIPS 140-3 Security Level 3 certified (upgraded from FIPS 140-2 in May 2023).
- seamlessly integrates with several AWS services to make encrypting data in those services easy.
- supports multi-region keys, which are AWS KMS keys in different AWS Regions. Multi-Region keys are not global and each multi-region key needs to be replicated and managed independently.
- supports External Key Store (XKS) capability (November 2022) allowing customers to store and control encryption keys on-premises or outside AWS cloud while using AWS KMS.
- provides three key store options: Default KMS key store, CloudHSM custom key store, and External key store (XKS).
CloudHSM
- provides secure cryptographic key storage to customers by making hardware security modules (HSMs) available in the AWS cloud
- helps manage your own encryption keys using FIPS 140-3 Level 3 validated HSMs (upgraded from FIPS 140-2).
- single tenant, dedicated physical device to securely generate, store, and manage cryptographic keys used for data encryption
- are inside the VPC (not EC2-classic) & isolated from the rest of the network
- can use VPC peering to connect to CloudHSM from multiple VPCs
- integrated with Amazon Redshift and Amazon RDS for Oracle
- EBS volume encryption, S3 object encryption and key management can be done with CloudHSM but requires custom application scripting
- is NOT fault-tolerant and would need to build a cluster as if one fails all the keys are lost
- enables quick scaling by adding and removing HSM capacity on-demand, with no up-front costs.
- automatically load balance requests and securely duplicates keys stored in any HSM to all of the other HSMs in the cluster.
- expensive, prefer AWS Key Management Service (KMS) if cost is a criteria.
AWS Payment Cryptography
- is a managed service for payment processing cryptographic operations (launched June 2023).
- provides payment-specific HSMs that replace on-premises payment hardware security modules.
- helps meet PCI (Payment Card Industry) security requirements and compliance needs.
- supports cryptographic operations like PIN generation, validation, and credit/debit card security code processing.
- manages underlying physical HSM infrastructure and key management automatically.
- integrates with AWS IAM for authorization and AWS CloudTrail for auditing.
- enables payment processing workloads to move to the cloud securely.
- provides elastic scaling for payment cryptography operations.
AWS Private Certificate Authority (Private CA)
- is a managed private certificate authority service for issuing and managing private SSL/TLS certificates.
- removes upfront investment and ongoing maintenance costs of operating your own private CA.
- supports two operating modes: General-purpose mode (certificates with any validity period) and Short-lived certificate mode (certificates valid up to 7 days, launched February 2023).
- integrates with AWS Certificate Manager (ACM) for automated certificate provisioning and renewal.
- supports Private CA Connector for Active Directory (September 2023) enabling AWS Private CA as drop-in replacement for self-managed enterprise CAs without local agents.
- provides audit and compliance support through AWS CloudTrail integration.
- enables certificate-based authentication for services like Amazon WorkSpaces.
AWS WAF
- is a web application firewall that helps monitor the HTTP/HTTPS traffic and allows controlling access to the content.
- helps protect web applications from attacks by allowing rules configuration that allow, block, or monitor (count) web requests based on defined conditions. These conditions include IP addresses, HTTP headers, HTTP body, URI strings, SQL injection and cross-site scripting.
- helps define Web ACLs, which is a combination of Rules that is a combinations of Conditions and Action to block or allow
- integrated with CloudFront, Application Load Balancer (ALB), API Gateway services commonly used to deliver content and applications
- supports custom origins outside of AWS, when integrated with CloudFront
- provides AWS WAF Fraud Control with three capabilities:
- Account Takeover Prevention (ATP) – Launched February 2022, protects login pages against credential stuffing attacks
- Account Creation Fraud Prevention (ACFP) – Launched June 2023, detects and blocks automated bot-based account creation
- Bot Control – Detects and controls common bots and targeted bots that use advanced evasion techniques
- supports Challenge and CAPTCHA actions for bot mitigation at no additional cost with Fraud Control.
- offers usage-based tiered pricing for Fraud Control (introduced June 2023).
AWS Verified Access
- provides VPN-less, secure access to corporate applications (GA April 2023).
- implements Zero Trust security model for application access without traditional VPN.
- validates each application request against identity and device security requirements before granting access.
- integrates with identity providers (IdPs) and device management systems for authentication and authorization.
- uses Cedar policy language for fine-grained access control policies.
- supports AWS WAF integration for additional web application protection.
- provides signed identity context to end applications for additional security.
- simplifies remote access management and improves user experience compared to VPN.
- eliminates VPN infrastructure management overhead.
Amazon Verified Permissions
- is a fully managed fine-grained authorization service for custom applications (GA June 2023).
- uses Cedar, an open-source policy language released May 2023, for defining authorization policies.
- enables developers to externalize authorization logic from application code.
- provides centralized policy management and administration.
- offers millisecond-latency authorization decisions with provably correct results.
- supports policy validation using automated reasoning to prevent misconfigurations.
- integrates with identity providers for user and group information.
- enables fine-grained permissions based on user attributes, resource attributes, and context.
- provides policy versioning and audit capabilities.
- follows “explicit permit” and “forbid overrides permit” principles.
AWS Secrets Manager
- helps protect secrets needed to access applications, services, and IT resources.
- enables you to easily rotate, manage, and retrieve database credentials, API keys, and other secrets throughout their lifecycle.
- secure secrets by encrypting them with encryption keys managed using AWS KMS.
- offers native secret rotation with built-in integration for RDS, Redshift, and DocumentDB.
- supports Lambda functions to extend secret rotation to other types of secrets, including API keys and OAuth tokens.
- supports IAM and resource-based policies for fine-grained access control to secrets and centralized secret rotation audit for resources in the AWS Cloud, third-party services, and on-premises.
- enables secret replication in multiple AWS regions (launched March 2021) to support multi-region applications and disaster recovery scenarios.
- automatically keeps replica secrets in sync with primary secret including rotation.
- supports private access using VPC Interface endpoints
AWS Shield
- is a managed service that provides protection against Distributed Denial of Service (DDoS) attacks for applications running on AWS
- provides protection for all AWS customers against common and most frequently occurring infrastructure (layer 3 and 4) attacks like SYN/UDP floods, reflection attacks, and others to support high availability of applications on AWS.
- provides AWS Shield Advanced with additional protections against more sophisticated and larger attacks for applications running on EC2, ELB, CloudFront, AWS Global Accelerator, and Route 53.
AWS GuardDuty
- offers threat detection that enables continuous monitoring and protects the AWS accounts and workloads.
- is a Regional service
- analyzes continuous streams of meta-data generated from AWS accounts and network activity found in AWS CloudTrail Events, EKS audit logs, VPC Flow Logs, and DNS Logs.
- integrated threat intelligence
- combines machine learning, anomaly detection, network monitoring, and malicious file discovery, utilizing both AWS-developed and industry-leading third-party sources to help protect workloads and data on AWS
- supports suppression rules, trusted IP lists, and thread lists.
- provides Malware Protection to detect malicious files on EBS volumes
- provides EKS Runtime Monitoring (March 2023) using fully managed EKS add-on for visibility into container runtime activities (file access, process execution, network connections).
- provides RDS Protection (March 2023) for profiling and monitoring access activity to Amazon Aurora databases.
- provides Lambda Protection for monitoring AWS Lambda function invocations and runtime behavior.
- can identify specific containers within EKS clusters that are potentially compromised and detect privilege escalation attempts.
- operates completely independently from the resources so there is no risk of performance or availability impacts on the workloads.
Amazon Inspector
- is a vulnerability management service that continuously scans the AWS workloads for vulnerabilities
- automatically discovers and scans EC2 instances and container images residing in Elastic Container Registry (ECR) for software vulnerabilities and unintended network exposure.
- supports AWS Lambda function scanning for vulnerabilities in application code and dependencies.
- provides CI/CD integration (November 2023) with open-source plugins for Jenkins, TeamCity, and other CI/CD tools to scan container images at build time.
- enables vulnerability scanning directly from CI/CD pipelines wherever they are running without activating Inspector service.
- scans Lambda functions on each deployment or update of application code or dependencies.
- creates a finding, when a software vulnerability or network issue is discovered, that describes the vulnerability, rates its severity, identifies the affected resource, and provides remediation guidance.
- is a Regional service.
- requires Systems Manager (SSM) agent to be installed and enabled for EC2 scanning.
Amazon Security Lake
- is a fully managed security data lake service (GA November 2023).
- automatically centralizes security data from AWS environments, SaaS providers, on-premises, and cloud sources into a purpose-built data lake.
- normalizes security data into the Open Cybersecurity Schema Framework (OCSF) standard format.
- aggregates data from AWS services like CloudTrail, VPC Flow Logs, Route 53 logs, and third-party sources.
- enables comprehensive security data analysis across entire organization.
- automatically collects data for existing and new accounts with multi-account support.
- stores security data in customer’s own AWS account for data ownership and control.
- integrates with analytics tools like Amazon Athena, Amazon OpenSearch, and third-party SIEM solutions.
- supports cross-region data aggregation for centralized security monitoring.
- pricing based on data ingestion volume and normalization (no charge for third-party or custom data).
Amazon Detective
- helps analyze, investigate, and quickly identify the root cause of potential security issues or suspicious activities.
- automatically collects log data from the AWS resources and uses machine learning, statistical analysis, and graph theory to build a linked set of data to easily conduct faster and more efficient security investigations.
- enables customers to view summaries and analytical data associated with CloudTrail logs, EKS audit logs, VPC Flow Logs.
- provides detailed summaries, analysis, and visualizations of the behaviors and interactions amongst your AWS accounts, EC2 instances, AWS users, roles, and IP addresses.
- maintains up to a year of aggregated data
- is a Regional service and needs to be enabled on a region-by-region basis.
- is a multi-account service that aggregates data from monitored member accounts under a single administrative account within the same region.
- has no impact on the performance or availability of the AWS infrastructure since it retrieves the log data and findings directly from the AWS services.
AWS Security Hub
- a cloud security posture management service that performs security best practice checks, aggregates alerts, and enables automated remediation.
- collects security data from across AWS accounts, services, and supported third-party partner products and helps you analyze your security trends and identify the highest priority security issues.
- is Regional abut supports cross-region aggregation of findings.
- automatically runs continuous, account-level configuration and security checks based on AWS best practices and industry standards which include CIS Foundations, PCI DSS.
- consolidates the security findings across accounts and provider products and displays results on the Security Hub console.
- supports integration with Amazon EventBridge. Custom actions can be defined when a finding is received.
- has multi-account management through AWS Organizations integration, which allows delegating an administrator account for the organization.
- works with AWS Config to perform most of its security checks for controls
AWS Macie
- Macie is a data security service that discovers sensitive data by using machine learning and pattern matching, provides visibility into data security risks, and enables automated protection against those risks.
- provides an inventory of the S3 buckets and automatically evaluates and monitors the buckets for security and access control.
- automates the discovery, classification, and reporting of sensitive data.
- generates a finding for you to review and remediate as necessary if it detects a potential issue with the security or privacy of the data, such as a bucket that becomes publicly accessible.
- provides multi-account support using AWS Organizations to enable Macie across all of the accounts.
- is a regional service and must be enabled on a region-by-region basis and helps view findings across all the accounts within each Region.
- supports VPC Interface Endpoints to access Macie privately from a VPC without an internet gateway, NAT device, VPN connection, or AWS Direct Connect connection.
AWS Artifact
- is a self-service audit artifact retrieval portal that provides customers with on-demand access to AWS’ compliance documentation and agreements
- can use AWS Artifact Reports to download AWS security and compliance documents, such as AWS ISO certifications, Payment Card Industry (PCI), and System and Organization Control (SOC) reports.
AWS Security Services – Practice Questions
- A company needs to manage encryption keys with FIPS 140-3 Level 3 compliance and wants AWS to handle the infrastructure. Which service should they use?
- A. AWS CloudHSM
- B. AWS KMS ✓
- C. AWS Secrets Manager
- D. AWS Certificate Manager
- A financial institution needs to process payment card transactions in the cloud while meeting PCI compliance requirements. Which service should they use?
- A. AWS CloudHSM
- B. AWS KMS
- C. AWS Payment Cryptography ✓
- D. AWS Private CA
- A company wants to provide secure access to corporate applications without using VPN. Which service implements Zero Trust access?
- A. AWS Client VPN
- B. AWS Verified Access ✓
- C. AWS Direct Connect
- D. AWS PrivateLink
- A development team needs to externalize authorization logic from their application and use fine-grained permissions. Which service should they use?
- A. AWS IAM
- B. Amazon Cognito
- C. Amazon Verified Permissions ✓
- D. AWS IAM Identity Center
- A company needs to centralize security data from multiple AWS accounts and third-party sources for analysis. Which service should they use?
- A. AWS Security Hub
- B. Amazon Security Lake ✓
- C. Amazon Detective
- D. AWS CloudTrail
- Which AWS service can detect runtime threats in EKS containers including file access and process execution?
- A. Amazon Inspector
- B. AWS Security Hub
- C. Amazon GuardDuty ✓
- D. Amazon Detective
- A company wants to scan container images for vulnerabilities in their CI/CD pipeline before deployment. Which service supports this?
- A. AWS Config
- B. Amazon Inspector ✓
- C. AWS Security Hub
- D. Amazon GuardDuty
- Which service can protect login pages from credential stuffing attacks and account takeover attempts?
- A. AWS Shield
- B. AWS WAF Fraud Control ✓
- C. Amazon GuardDuty
- D. AWS Firewall Manager
- A company needs to replicate secrets across multiple regions for disaster recovery. Which service supports this?
- A. AWS Systems Manager Parameter Store
- B. AWS Secrets Manager ✓
- C. AWS KMS
- D. AWS Certificate Manager
- Which service was renamed from AWS Single Sign-On (SSO) in July 2022?
- A. AWS IAM
- B. Amazon Cognito
- C. AWS IAM Identity Center ✓
- D. AWS Directory Service