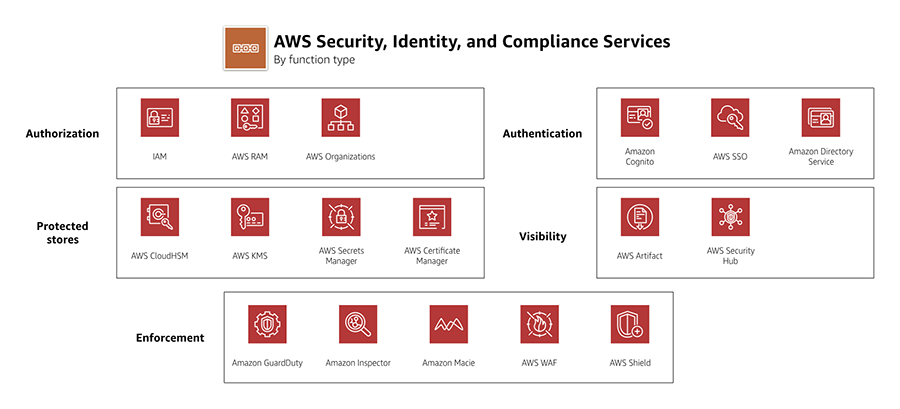
AWS Security Hub
- AWS Security Hub is a cloud security posture management service that performs security best practice checks, aggregates alerts, and enables automated remediation.
- collects security data from across AWS accounts, services, and supported third-party partner products and helps analyze the security trends and identify the highest priority security issues.
- is Regional and only receives and processes findings from the Region where the Security Hub is enabled. However, it supports cross-region aggregation of findings via the designation of an aggregator region.
- must be enabled in each region to view findings in that region.
- automatically runs continuous, account-level configuration and security checks based on AWS best practices and industry standards which include
- CIS AWS Foundations
- Payment Card Industry Data Security Standard (PCI DSS)
- AWS Foundational Security Best Practices
- can consume, aggregate, organize, and prioritize findings from
- AWS services like
- Amazon GuardDuty,
- Amazon Inspector,
- Amazon Macie,
- AWS IAM Access Analyzer,
- AWS Firewall Manager
- other supported third-party partner products.
- AWS services like
- consolidates the security findings across accounts and provider products and displays results on the Security Hub console.
- supports integration with Amazon EventBridge. Custom actions can be defined when a finding is received.
- only detects and consolidates findings that are generated after the Security Hub is enabled.
- has multi-account management through AWS Organizations integration, which allows delegating an administrator account for the organization.
- uses service-linked AWS Config rules to perform most of its security checks for controls. AWS Config must be enabled on all accounts – both the administrator account and member accounts – in each Region where Security Hub is enabled.
- works with a service-linked role named
AWSServiceRoleForSecurityHubwhich includes the permissions and trust policy to do the following:- Detect and aggregate findings from Amazon GuardDuty, Amazon Inspector, and Amazon Macie
- Configure the requisite AWS Config infrastructure to run security checks for the supported standards

AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- A security engineer has been asked to continuously monitor the company’s AWS account using automated compliance checks based on AWS best practices and Center for Internet Security (CIS) AWS Foundations Benchmarks. How can the security engineer accomplish this using AWS services?
- AWS Config + AWS Security Hub
- Amazon Inspector + AWS GuardDuty
- Amazon Inspector + AWS Shield
- AWS Config + Amazon Inspector