AWS Network Load Balancer – NLB
- Network Load Balancer – NLB operates at the connection level (Layer 4), routing connections to targets – EC2 instances, and containers based on IP protocol data.
- NLB is suited for load balancing of TCP traffic
- NLB is capable of handling millions of requests per second while maintaining ultra-low latencies (~100 ms vs 400 ms for ALB)
- NLB is optimized to handle sudden and volatile traffic patterns while using a single static IP address per Availability Zone.
- NLB also supports TLS termination, preserves the source IP of the clients, and provides stable IP support and Zonal isolation.
- NLB supports long-running connections that are very useful for WebSocket-type applications.
- NLB is integrated with other AWS services such as Auto Scaling, EC2 Container Service (ECS), and CloudFormation.
- NLB supports connections from clients over VPC peering, AWS-managed VPN, and third-party VPN solutions.
- For TCP traffic,
- the load balancer selects a target using a flow hash algorithm based on the protocol, source IP address, source port, destination IP address, destination port, and TCP sequence number.
- TCP connections from a client having different source ports and sequence numbers and can be routed to different targets.
- Each individual TCP connection is routed to a single target for the life of the connection.
- For UDP traffic,
- the load balancer selects a target using a flow hash algorithm based on the protocol, source IP address, source port, destination IP address, and destination port.
- A UDP flow has the same source and destination, so it is consistently routed to a single target throughout its lifetime.
- Different UDP flows have different source IP addresses and ports, so they can be routed to different targets.
- back-end server authentication (MTLS) is not supported.
session stickiness is not supported
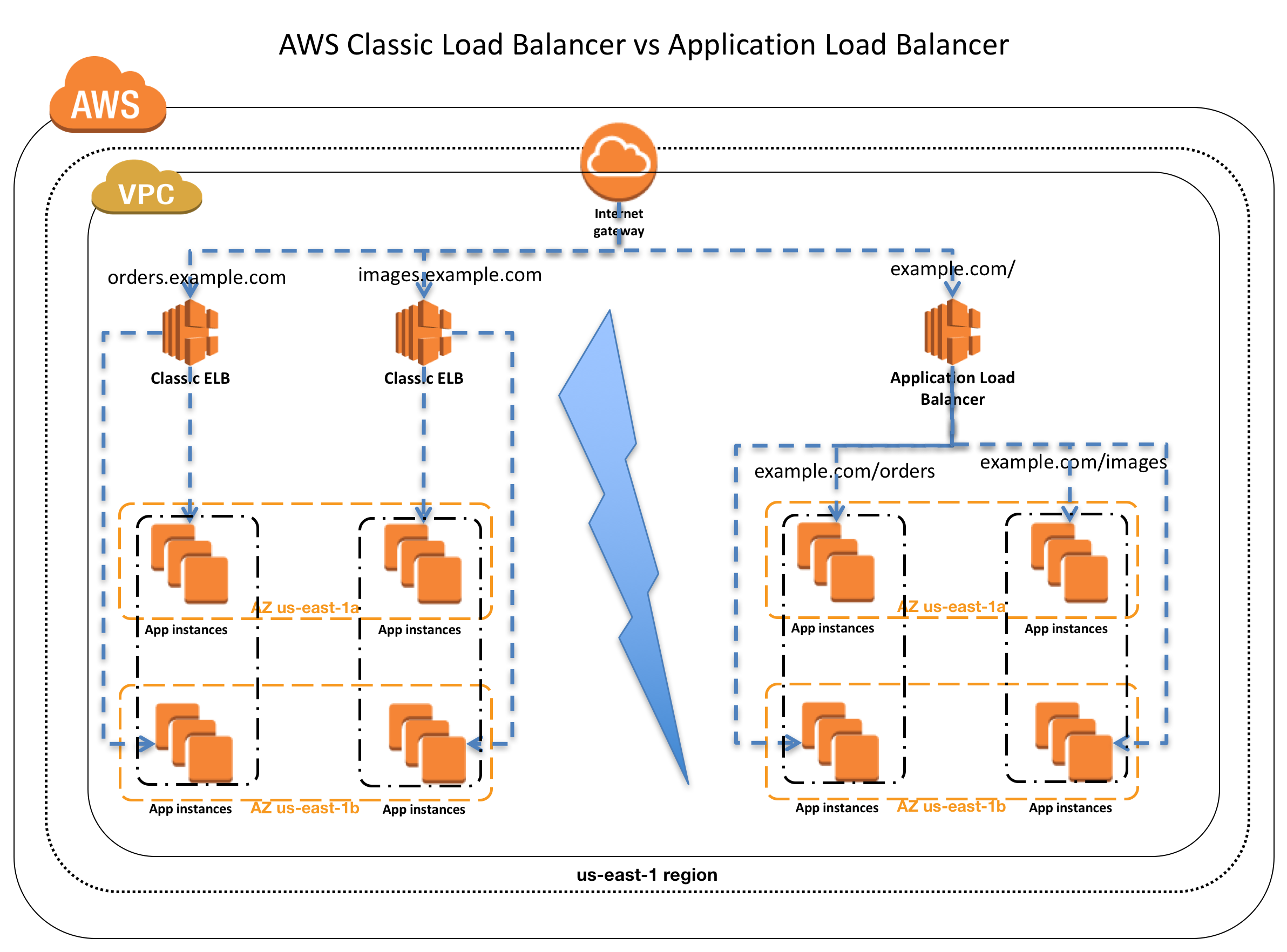
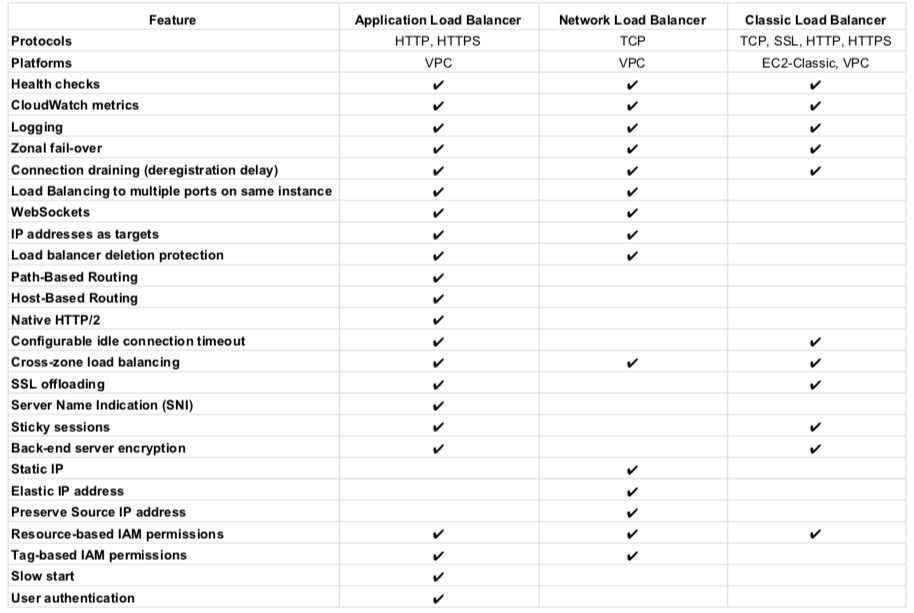
Classic Load Balancer vs Application Load Balancer vs Network Load Balancer
Refer Blog Post @ Classic Load Balancer vs Application Load Balancer vs Network Load Balancer
Network Load Balancer Features
Connection-based Layer 4 Load Balancing
- Allows load balancing of both TCP and UDP traffic, routing connections to targets – EC2 instances, microservices, and containers.
High Availability
- is highly available.
- accepts incoming traffic from clients and distributes this traffic across the targets within the same AZ (except for Cross-zone load balancing).
- monitors the health of its registered targets and routes the traffic only to healthy targets
- if a health check fails and an unhealthy target is detected, it stops routing traffic to that target and reroutes traffic to remaining healthy targets.
- if configured with multiple AZs and if all the targets in a single AZ fail, it routes traffic to healthy targets in the other AZs
Availability Zones
- can be used to route traffic across multiple Availability Zones.
- However, AZ must be enabled before the traffic is routed to that AZ.
- AZ can be enabled, even after the NLB creation.
- AZ once enabled, cannot be removed.
- Cross-zone load balancing works only for AZs enabled with NLB.
High Throughput
- is designed to handle traffic as it grows and can load balance millions of requests/sec.
- can also handle sudden volatile traffic patterns.
Low Latency
- offers extremely low latencies for latency-sensitive applications.
Cross Zone Load Balancing
- enables cross-zone loading balancing only after creating the NLB
- is disabled, by default, and charges apply for inter-az traffic.
- only works for the AZs that are enabled on the AZ
Sticky Sessions
- Sticky sessions (source IP affinity) are a mechanism to route requests from the same client to the same target.
- Stickiness is defined at the target group level
Load Balancing using IP addresses as Targets
- allows load balancing of any application hosted in AWS or on-premises using IP addresses of the application backends as targets.
- allows load balancing to an application backend hosted on any IP address and any interface on an instance.
- ability to load balance across AWS and on-premises resources help migrate-to-cloud, burst-to-cloud or failover-to-cloud.
- applications hosted in on-premises locations can be used as targets over a Direct Connect connection and EC2-Classic (using ClassicLink).
Preserve Source IP Address
- preserves client-side source IP allowing the back-end to see the client IP address.
- Target groups can be created with target type as instance ID or IP address.
- If targets are registered by instance ID or ECS tasks, the source IP addresses of the clients are preserved and provided to the applications.
- If targets are registered by IP address
- for TCP & TLS, the source IP addresses are the private IP addresses of the load balancer nodes. Use Proxy Protocol.
- for UDP & TCP_UDP, it is enabled by default and the source IP addresses of the clients are preserved.
Static IP support
- automatically provides a static IP per Availability Zone (subnet) that can be used by applications as the front-end IP of the load balancer.
- creates a network interface for each enabled AZ. Each load balancer node in the AZ uses this network interface to get a static IP address.
- Internet-facing load balancer can optionally associate one Elastic IP address per subnet.
Elastic IP support
- an Elastic IP per Availability Zone (subnet) can also be assigned, optionally, thereby providing a fixed IP.
Health Checks
- supports both network and application target health checks using HTTP, HTTPS, and TCP.
- Network-level health check
- is based on the overall response of the underlying target (instance or a container) to normal traffic.
- target is marked unavailable if it is slow or unable to respond to new connection requests
- Application-level health check
- is based on a specific URL on a given target to test the application health deeper
DNS Fail-over
- integrates with Route 53
- Route 53 will direct traffic to load balancer nodes in other AZs, if there are no healthy targets with NLB or if the NLB itself is unhealthy
- if NLB is unresponsive, Route 53 will remove the unavailable load balancer IP address from service and direct traffic to an alternate Network Load Balancer in another region.
Integration with AWS Services
- is integrated with other AWS services such as Auto Scaling, EC2 Container Service (ECS), CloudFormation, CodeDeploy, and AWS Config.
Long-lived TCP Connections
- supports long-lived TCP connections ideal for WebSocket-type of applications
Central API Support
- uses the same API as Application Load Balancer.
- enables you to work with target groups, health checks, and load balance across multiple ports on the same EC2 instance to support containerized applications.
Robust Monitoring and Auditing
- integrated with CloudWatch to report Network Load Balancer metrics.
- CloudWatch provides metrics such as Active Flow count, Healthy Host Count, New Flow Count, Processed bytes, and more.
- integrated with CloudTrail to track API calls to the NLB
Enhanced Logging
- Flow Logs feature helps record all requests sent to the load balancer.
- Flow Logs capture information about the IP traffic going to and from network interfaces in the VPC.
- Flow log data is stored using CloudWatch Logs.
Zonal Isolation
- is designed for application architectures in a single zone.
- can be enabled in a single AZ to support architectures that require zonal isolation
- automatically fails-over to other healthy AZs, if something fails in an AZ
- it’s recommended to configure the load balancer and targets in multiple AZs for achieving high availability
Zonal DNS Name
- supports DNS names for each of its nodes.
- by default, resolving the Regional NLB DNS name returns the IP address for all NLB nodes in all enabled AZs.
- can be used to determine the IP address of each node.
- useful to minimize latency and inter-az data transfer costs.
Advantages over Classic Load Balancer
- Ability to handle volatile workloads and scale to millions of requests per second, without the need of pre-warming
- Support for static IP/Elastic IP addresses for the load balancer
- Support for registering targets by IP address, including targets outside the VPC (on-premises) for the load balancer.
- Support for routing requests to multiple applications on a single EC2 instance. A single instance or IP address can be registered with the same target group using multiple ports.
- Support for containerized applications. Using Dynamic port mapping, ECS can select an unused port when scheduling a task and register the task with a target group using this port.
- Support for monitoring the health of each service independently, as health checks are defined at the target group level and many CloudWatch metrics are reported at the target group level. Attaching a target group to an Auto Scaling group enables scaling each service dynamically based on demand
Network Load Balancer Limitations
- can’t associate Security Groups with NLBs
- can’t disable/remove an AZ once you enable it.
- can’t modify ENIs created by NLB in each AZ
- can’t change EIPs and Private IPs attached to the ENIs after NLB creation.
- can’t register EC2 instances by instance ID for instances in another VPC even if VPC peering is done.
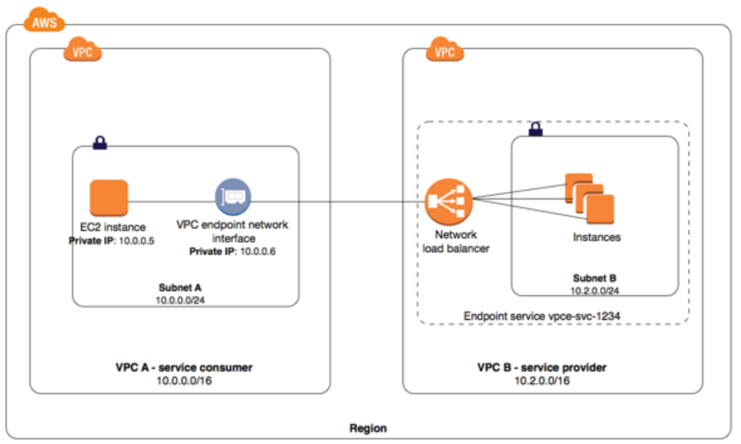
Network Load Balancer with AWS PrivateLink
- Interface Endpoints can be used to create custom applications in VPC and configure them as an AWS PrivateLink-powered service (referred to as an endpoint service) exposed through a Network Load Balancer. The custom applications can be hosted within AWS or on-premises.
Network Load Balancer Pricing
- charged for each hour or partial hour that an NLB is running and the number of Load Balancer Capacity Units (LCU) used per hour.
- An LCU is a new metric for determining NLB pricing
- An LCU defines the maximum resource consumed in any one of the dimensions (new connections/flows, active connections/flows, bandwidth and rule evaluations) the Network Load Balancer processes your traffic.
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- A company wants to use load balancer for their application. However, the company wants to forward the requests without any header modification. What service should the company use?
- Classic Load Balancer
- Network Load Balancer
- Application Load Balancer
- Use Route 53
- A company is hosting an application in AWS for third party access. The third party needs to whitelist the application based on the IP. Which AWS service can the company use in the whitelisting of the IP address?
- AWS Application Load Balancer
- AWS Classic Load balancer
- AWS Network Load Balancer
- AWS Route 53
References
AWS Documentation – ELB_Network_Load_Balancer