Table of Contents
hide
Encrypting Data at Rest
- AWS delivers a secure, scalable cloud computing platform with high availability, offering the flexibility for you to build a wide range of applications
- AWS allows several options for encrypting data at rest, for additional layer of security, ranging from completely automated AWS encryption solution to manual client-side options
- Encryption requires 3 things
- Data to encrypt
- Encryption keys
- Cryptographic algorithm method to encrypt the data
- AWS provides different models for Securing data at rest on the following parameters
- Encryption method
- Encryption algorithm selection involves evaluating security, performance, and compliance requirements specific to your application
- Key Management Infrastructure (KMI)
- KMI enables managing & protecting the encryption keys from unauthorized access
- KMI provides
- Storage layer that protects plain text keys
- Management layer that authorize key usage
- Encryption method
- Hardware Security Module (HSM)
- Common way to protect keys in a KMI is using HSM
- An HSM is a dedicated storage and data processing device that performs cryptographic operations using keys on the device.
- An HSM typically provides tamper evidence, or resistance, to protect keys from unauthorized use.
- A software-based authorization layer controls who can administer the HSM and which users or applications can use which keys in the HSM
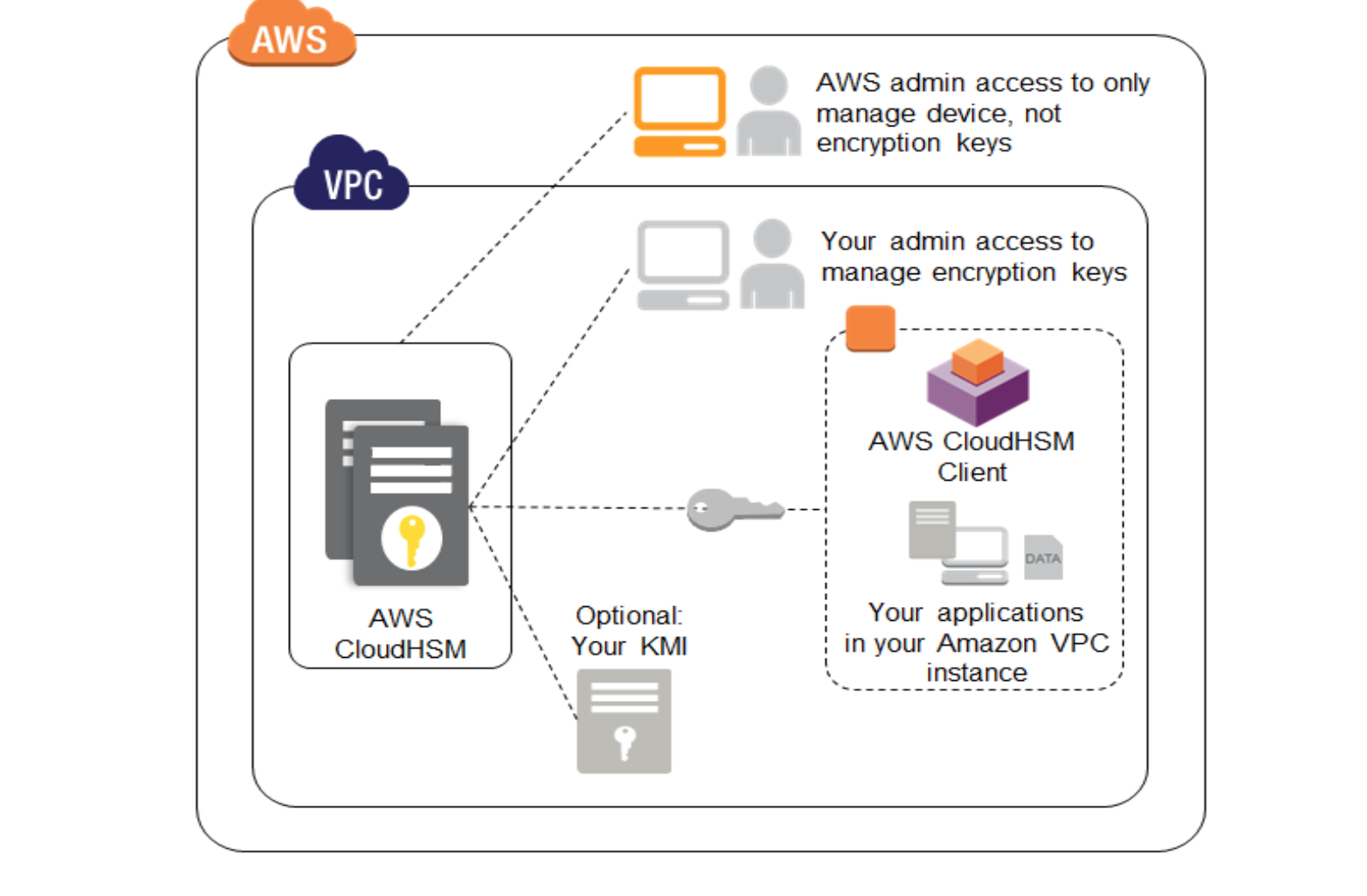
- AWS CloudHSM
- AWS CloudHSM appliance has both physical and logical tamper detection and response mechanisms that trigger zeroization of the appliance.
- Zeroization erases the HSM’s volatile memory where any keys in the process of being decrypted were stored and destroys the key that encrypts stored objects, effectively causing all keys on the HSM to be inaccessible and unrecoverable.
- AWS CloudHSM can be used to generate and store key material and can perform encryption and decryption operations,
- AWS CloudHSM, however, does not perform any key lifecycle management functions (e.g., access control policy, key rotation) and needs a compatible KMI.
- KMI can be deployed either on-premises or within Amazon EC2 and can communicate to the AWS CloudHSM instance securely over SSL to help protect data and encryption keys.
- AWS CloudHSM service uses SafeNet Luna appliances, any key management server that supports the SafeNet Luna platform can also be used with AWS CloudHSM
- AWS Key Management Service (KMS)
- AWS KMS is a managed encryption service that allows you to provision and use keys to encrypt data in AWS services and your applications.
- Masters key, after creation, are designed to never be exported from the service.
- AWS KMS gives you centralized control over who can access your master keys to encrypt and decrypt data, and it gives you the ability to audit this access.
- Data can be sent into the KMS to be encrypted or decrypted under a specific master key under you account.
- AWS KMS is natively integrated with other AWS services (for e.g. Amazon EBS, Amazon S3, and Amazon Redshift) and AWS SDKs to simplify encryption of your data within those services or custom applications
- AWS KMS provides global availability, low latency, and a high level of durability for your keys.
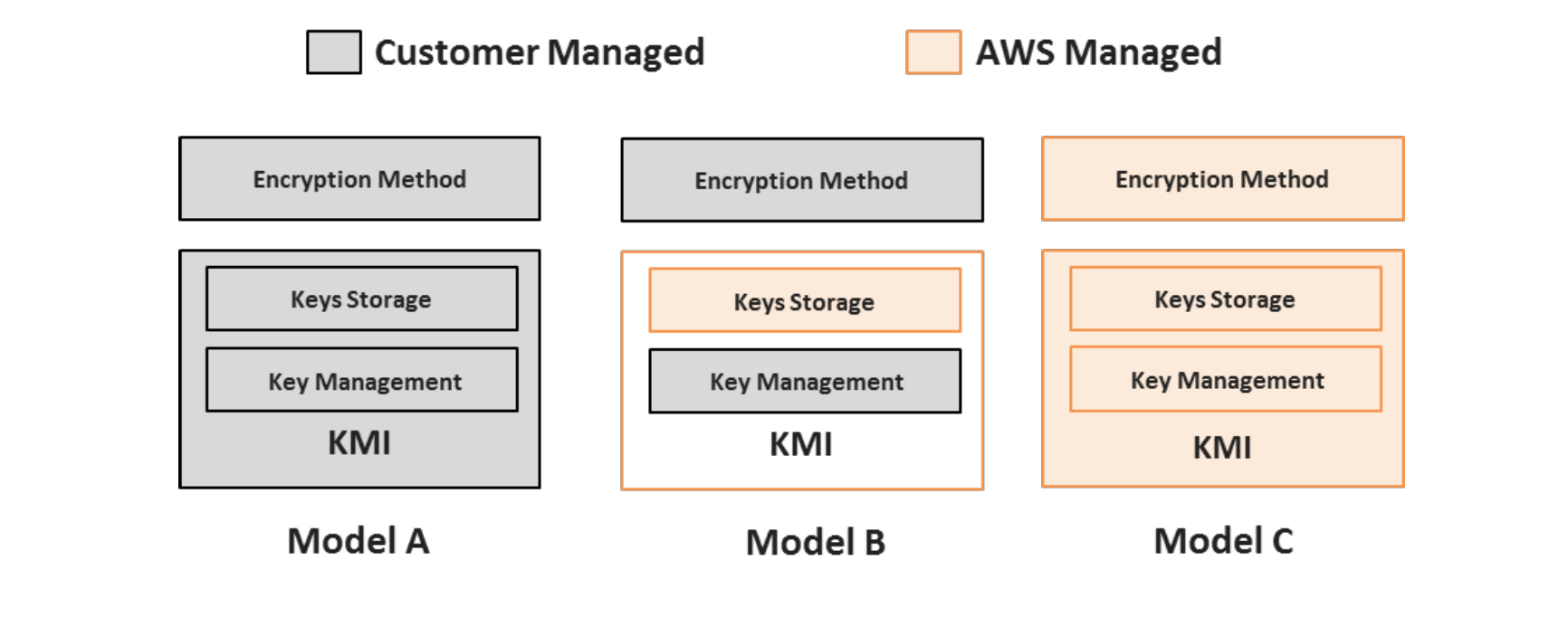
Encryption Models in AWS
Encryption models in AWS depends on the on how you/AWS provides the encryption method and the KMI
- You control the encryption method and the entire KMI
- You control the encryption method, AWS provides the storage component of the KMI, and you provide the management layer of the KMI.
- AWS controls the encryption method and the entire KMI.
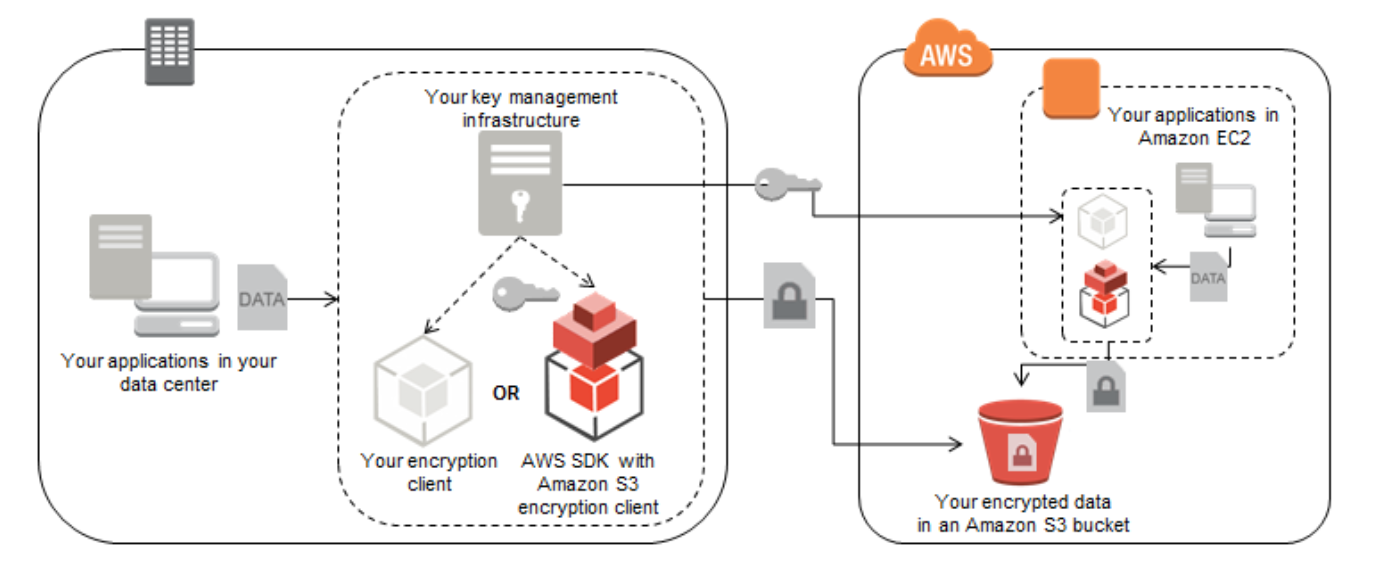
Model A: You control the encryption method and the entire KMI
- You use your own KMI to generate, store, and manage access to keys as well as control all encryption methods in your applications
- Proper storage, management, and use of keys to ensure the confidentiality, integrity, and availability of your data is your responsibility
- AWS has no access to your keys and cannot perform encryption or decryption on your behalf.
- Amazon S3
- Encryption of the data is done before the object is sent to AWS S3
- Encryption of the data can be done using any encryption method and the encrypted data can be uploaded using the PUT request in the Amazon S3 API
- Key used to encrypt the data needs to be stored securely in your KMI
- To decrypt this data, the encrypted object can be downloaded from Amazon S3 using the GET request in the Amazon S3 API and then decrypted using the key in your KMI
- AWS provide Client-side encryption handling, where you can provide your key to the AWS S3 encryption client which will encrypt and decrypt the data on your behalf. However, AWS never has access to the keys or the unencrypted data
- Amazon EBS
- Amazon Elastic Block Store (Amazon EBS) provides block-level storage volumes for use with Amazon EC2 instances. Amazon EBS volumes are network-attached, and persist independently from the life of an instance.
- Because Amazon EBS volumes are presented to an instance as a block device, you can leverage most standard encryption tools for file system-level or block-level encryption
- Block level encryption
- Block level encryption tools usually operate below the file system layer using kernel space device drivers to perform encryption and decryption of data.
- These tools are useful when you want all data written to a volume to be encrypted regardless of what directory the data is stored in
- File System level encryption
- File system level encryption usually works by stacking an encrypted file system on top of an existing file system.
- This method is typically used to encrypt a specific directory
- These solutions require you to provide keys, either manually or from your KMI.
- Both block-level and file system-level encryption tools can only be used to encrypt data volumes that are not Amazon EBS boot volumes, as they don’t allow you to automatically make a trusted key available to the boot volume at startup
- There are third party solutions available, which can help encrypt both the boot and data volumes as well as supplying and protecting keys
- AWS Storage Gateway
- AWS Storage Gateway is a service connecting an on-premises software appliance with Amazon S3. Data on disk volumes attached to the AWS Storage Gateway will be automatically uploaded to Amazon S3 based on policy
- Encryption of the source data on the disk volumes can be either done before writing to the disk or using block level encryption on the iSCSI endpoint that AWS Storage Gateway exposes to encrypt all data on the disk volume.
- Amazon RDS
- Amazon RDS doesn’t expose the attached disk it uses for data storage, transparent disk encryption using techniques for EBS section cannot be applied.
- However, individual fields data can be encrypted before the data is written to RDS and decrypted after reading it.
Model B: You control the encryption method, AWS provides the KMI storage component, and you provide the KMI management layer
- Model B is similar to Model A where the encryption method is managed by you
- Model B differs in the approach to Model A where the keys are maintained in AWS CloudHSM rather than than the on-premise key storage system
- Only you have access to the cryptographic partitions within the dedicated HSM to use the keys
Model C: AWS controls the encryption method and the entire KMI
- AWS provides and manages the server-side encryption of your data, transparently managing the encryption method and the keys.
- AWS KMS and other services that encrypt your data directly use a method called envelope encryption to provide a balance between performance and security.
- Envelope Encryption method
- A master key is defined either by you or AWS
- A data key (data encryption key) is generated by the AWS service at the time when data encryption is requested
- Data key is used to encrypt your data.
- Data key is then encrypted with a key-encrypting key (master key) unique to the service storing your data.
- Encrypted data key and the encrypted data are then stored by the AWS storage service on your behalf.
- Master key (key-encrypting keys) used to encrypt data keys are stored and managed separately from the data and the data keys
- For decryption of the data, the process is reversed. Encrypted data key is decrypted using the key-encrypting key; the data key is then used to decrypt your data
- Authorized use of encryption keys is done automatically and is securely managed by AWS.
- Because unauthorized access to those keys could lead to the disclosure of your data, AWS has built systems and processes with strong access controls that minimize the chance of unauthorized access and had these systems verified by third-party audits to achieve security certifications including SOC 1, 2, and 3, PCI-DSS, and FedRAMP.
- Amazon S3
- SSE-S3
- AWS encrypts each object using a unique data key
- Data key is encrypted with a periodically rotated master key managed by S3
- Amazon S3 server-side encryption uses 256-bit Advanced Encryption Standard (AES) keys for both object and master keys
- SSE-KMS
- Master keys are defined and managed in KMS for your account
- Object Encryption
- When an object is uploaded, a request is sent to KMS to create an object key.
- KMS generates a unique object key and encrypts it using the master key; KMS then returns this encrypted object key along with the plaintext object key to Amazon S3.
- Amazon S3 web server encrypts your object using the plaintext object key and stores the now encrypted object (with the encrypted object key) and deletes the plaintext object key from memory.
- Object Decryption
- To retrieve the encrypted object, Amazon S3 sends the encrypted object key to AWS KMS.
- AWS KMS decrypts the object key using the correct master key and returns the decrypted (plaintext) object key to S3.
- Amazon S3 decrypts the encrypted object, with the plaintext object key, and returns it to you.
- SSE-C
- Amazon S3 is provided an encryption key, while uploading the object
- Encryption key is used by Amazon S3 to encrypt your data using AES-256
- After object encryption, Amazon S3 deletes the encryption key
- For downloading, you need to provide the same encryption key, which AWS matches, decrypts and returns the object
- SSE-S3
- Amazon EBS
- When Amazon EBS volume is created, you can choose the master key in KMS to be used for encrypting the volume
- Volume encryption
- Amazon EC2 server sends an authenticated request to AWS KMS to create a volume key.
- AWS KMS generates this volume key, encrypts it using the master key, and returns the plaintext volume key and the encrypted volume key to the Amazon EC2 server.
- Plaintext volume key is stored in memory to encrypt and decrypt all data going to and from your attached EBS volume.
- Volume decryption
- When the encrypted volume (or any encrypted snapshots derived
from that volume) needs to be re-attached to an instance, a call is made to AWS KMS to decrypt the encrypted volume key. - AWS KMS decrypts this encrypted volume key with the correct master key and returns the decrypted volume key to Amazon EC2.
- When the encrypted volume (or any encrypted snapshots derived
- Amazon Glacier
- Glacier provide encryption of the data, by default
- Before it’s written to disk, data is always automatically encrypted using 256-bit AES keys unique to the Amazon Glacier service that are stored in separate systems under AWS control
- AWS Storage Gateway
- AWS Storage Gateway transfers your data to AWS over SSL
- AWS Storage Gateway stores data encrypted at rest in Amazon S3 or Amazon Glacier using their respective server side encryption schemes.
- Amazon RDS – Oracle
- Oracle Advanced Security option for Oracle on Amazon RDS can be used to leverage the native Transparent Data Encryption (TDE) and Native Network Encryption (NNE) features
- Oracle encryption module creates data and key-encrypting keys to encrypt the database
- Key-encrypting keys specific to your Oracle instance on Amazon RDS are themselves encrypted by a periodically rotated 256-bit AES master key.
- Master key is unique to the Amazon RDS service and is stored in separate systems under AWS control
- Amazon RDS -SQL server
- Transparent Data Encryption (TDE) can be provisioned for Microsoft SQL Server on Amazon RDS.
- SQL Server encryption module creates data and keyencrypting keys to encrypt the database.
- Key-encrypting keys specific to your SQL Server instance on Amazon RDS are themselves encrypted by a periodically rotated, regional 256-bit AES master key
- Master key is unique to the Amazon RDS service and is stored in separate systems under AWS control
Sample Exam Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- How can you secure data at rest on an EBS volume?
- Encrypt the volume using the S3 server-side encryption service
- Attach the volume to an instance using EC2’s SSL interface.
- Create an IAM policy that restricts read and write access to the volume.
- Write the data randomly instead of sequentially.
- Use an encrypted file system on top of the EBS volume
- Your company policies require encryption of sensitive data at rest. You are considering the possible options for protecting data while storing it at rest on an EBS data volume, attached to an EC2 instance. Which of these options would allow you to encrypt your data at rest? (Choose 3 answers)
- Implement third party volume encryption tools —
- Do nothing as EBS volumes are encrypted by default
- Encrypt data inside your applications before storing it on EBS
- Encrypt data using native data encryption drivers at the file system level
- Implement SSL/TLS for all services running on the server
- A company is storing data on Amazon Simple Storage Service (S3). The company’s security policy mandates that data is encrypted at rest. Which of the following methods can achieve this? Choose 3 answers
- Use Amazon S3 server-side encryption with AWS Key Management Service managed keys
- Use Amazon S3 server-side encryption with customer-provided keys
- Use Amazon S3 server-side encryption with EC2 key pair.
- Use Amazon S3 bucket policies to restrict access to the data at rest.
- Encrypt the data on the client-side before ingesting to Amazon S3 using their own master key
- Use SSL to encrypt the data while in transit to Amazon S3.
- Which 2 services provide native encryption
- Amazon EBS
- Amazon Glacier
- Amazon Redshift (is optional)
- Amazon RDS (is optional)
- Amazon Storage Gateway
- With which AWS services CloudHSM can be used (select 2)
- S3
- DynamoDb
- RDS
- ElastiCache
- Amazon Redshift
I believe Question(4) You meant Amazon EBS and Amazon Storage Gateway , please correct it or clarify.
Thanks
Its Glacier and Storage Gateway as they provide native encryption for the rest of the services they do provide the feature but is not enabled by default
Question #5. Why S3 is not the correct answer? The encryption keys for S3 can be stored and managed by cloudHSM.
Thats changed now as per the FAQs ..
AWS services do not integrate with CloudHSM directly today. If you want to use the server-side cryptography offered by many AWS services (such as EBS, S3, or RDS), you should consider the AWS Key Management Service. Over time we may integrate CloudHSM with other AWS services.
How sqs SSE encrypt message body using awssdk.sqs for .net ? Is KMS encryption works with rest only ?
Server Side encryption is now available for SQS. Refer AWS Post @ https://aws.amazon.com/blogs/aws/new-server-side-encryption-for-amazon-simple-queue-service-sqs/
Hi Jeyandra
Can you assist with this please?
decurity p0licy of an organization equires applic@tion to ncrypt data before writing to the disk
Which olution should organization use to meet requirement
AWS KMS API
AWS certificate manager
API gateway with sts
IAM access key
KMS can help you encrypt the data before writing to disk.
As from Nov 2018 DynamoDB has native encryption at rest
https://aws.amazon.com/about-aws/whats-new/2018/11/amazon-dynamodb-encrypts-all-customer-data-at-rest/
Thats right Vinicius. DynamoDB and SQS both support encryption now.
Cool