DynamoDB Security
- DynamoDB provides a highly durable storage infrastructure for mission-critical and primary data storage.
- Data is redundantly stored on multiple devices across multiple facilities in a DynamoDB Region.
- AWS handles basic security tasks like guest operating system (OS) and database patching, firewall configuration, and disaster recovery.
- DynamoDB protects user data stored at rest and in transit between on-premises clients and DynamoDB, and between DynamoDB and other AWS resources within the same AWS Region.
- Fine-Grained Access Control (FGAC) gives a high degree of control over data in the table.
- FGAC helps control who (caller) can access which items or attributes of the table and perform what actions (read/write capability).
- FGAC is integrated with IAM, which manages the security credentials and the associated permissions.
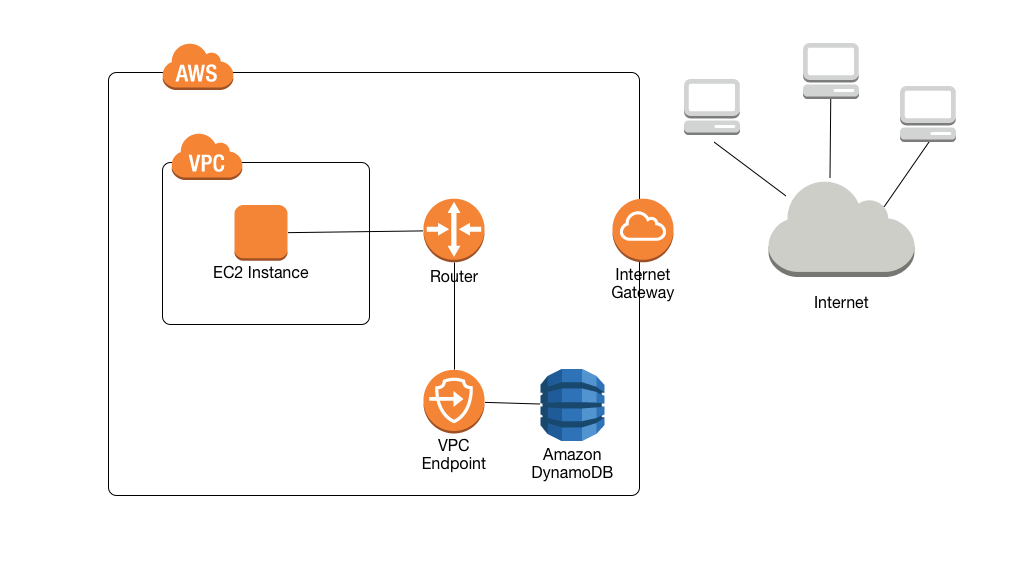
- VPC Endpoints allow private connectivity from within a VPC only to DynamoDB.
DynamoDB Resource-Based Policies – March 2024
- DynamoDB now supports resource-based policies to simplify access control for DynamoDB resources.
- Resource-based policies allow you to specify IAM principals that have access to a resource and what actions they can perform directly on the resource.
- Simplifies cross-account access without requiring IAM role assumption.
- Can be attached to:
- DynamoDB tables
- DynamoDB Streams
- Resource-based policies work alongside IAM identity policies for comprehensive access control.
- Enables fine-grained permissions at the resource level.
- Useful for scenarios like:
- Cross-account data sharing
- Third-party integrations
- Service-to-service access
DynamoDB Encryption
- DynamoDB Security supports both encryption at rest and in transit.
Encryption in Transit
- DynamoDB Data in Transit encryption can be done by encrypting sensitive data on the client side or using encrypted connections (TLS).
- DAX supports encryption in transit, ensuring that all requests and responses between the application and the cluster are encrypted by transport level security (TLS), and connections to the cluster can be authenticated by verification of a cluster x509 certificate.
- All the data in DynamoDB is encrypted in transit
- communications to and from DynamoDB using the HTTPS protocol, which protects network traffic using SSL/TLS encryption.
- Data can also be protected using client-side encryption
Encryption at Rest
- Encryption at rest enables encryption for the data persisted (data at rest) in the DynamoDB tables.
- Encryption at rest includes the base tables, primary key, local and global secondary indexes, streams, global tables, backups, and DynamoDB Accelerator (DAX) clusters.
- Encryption at rest is enabled on all DynamoDB table data and cannot be disabled.
- Encryption at rest automatically integrates with AWS KMS for managing the keys used for encrypting the tables.
- Encryption at rest also supports the following KMS keys
- AWS owned CMK – Default encryption type. The key is owned by DynamoDB (no additional charge).
- AWS managed CMK – the key is stored in your account and is managed by AWS KMS (AWS KMS charges apply).
- Customer managed CMK – the key is stored in your account and is created, owned, and managed by you. You have full control over the KMS key (AWS KMS charges apply).
- Encryption at rest can be enabled only for a new table and encryption keys can be switched for an existing table.
- DynamoDB streams can be used with encrypted tables and are always encrypted with a table-level encryption key.
- On-Demand Backups of encrypted DynamoDB tables are encrypted using S3’s Server-Side Encryption
- Encryption at rest encrypts the data using 256-bit AES encryption.
- DAX clusters cannot use customer-managed key encryption.
DynamoDB Encryption Client
- DynamoDB Encryption Client is a software library that helps protect the table data before sending it to DynamoDB.
- Encrypting the sensitive data in transit and at rest helps ensure that the plaintext data isn’t available to any third party, including AWS.
- helps in end-to-end data encryption.
- encrypts attribute values that can be controlled but do not encrypt the entire table, attribute names, or primary key.
VPC Endpoints
- By default, communications to and from DynamoDB use the HTTPS protocol, which protects network traffic by using SSL/TLS encryption.
- DynamoDB supports two types of VPC endpoints: Gateway Endpoints and Interface Endpoints (using AWS PrivateLink).
Gateway Endpoints
- A VPC gateway endpoint for DynamoDB enables EC2 instances in the VPC to use their private IP addresses to access DynamoDB with no exposure to the public internet.
- Traffic between the VPC and the AWS service does not leave the Amazon network.
- EC2 instances do not require public IP addresses, an internet gateway, a NAT device, or a virtual private gateway in the VPC.
- VPC Endpoint Policies to control access to DynamoDB.
- No additional charge for using gateway endpoints.
- Accessible only from within the VPC where they are created.
Interface Endpoints (AWS PrivateLink)
DynamoDB Interface Endpoints – March 2024
- DynamoDB now supports AWS PrivateLink with interface VPC endpoints.
- Interface endpoints are represented by elastic network interfaces (ENIs) with private IP addresses.
- Accessible from:
- Within the VPC
- On-premises networks via AWS Direct Connect or Site-to-Site VPN
- Other AWS Regions via VPC peering
- Eliminates need for public IP addresses, proxy infrastructure, or firewall rules for on-premises access.
- Supports private DNS names for simplified connectivity.
- Standard AWS PrivateLink charges apply.
DynamoDB Streams Interface Endpoints – March 2025
- DynamoDB Streams APIs now support AWS PrivateLink.
- Enables private access to DynamoDB Streams APIs without traversing the public internet.
- Supports GetRecords, GetShardIterator, and DescribeStream operations.
- Only interface endpoints are supported for DynamoDB Streams (gateway endpoints not supported).
DAX Interface Endpoints – October 2025
- DynamoDB Accelerator (DAX) now supports AWS PrivateLink.
- Enables secure access to DAX management APIs over private IP addresses.
- Supported APIs: CreateCluster, DescribeClusters, DeleteCluster.
- Accessible using private DNS names.
DynamoDB Security Best Practices
- DynamoDB encrypts at rest all user data stored in tables, indexes, streams, and backups using encryption keys stored in KMS.
- DynamoDB can be configured to use an AWS owned key (default encryption type), an AWS managed key, or a customer managed key to encrypt user data.
- Use customer-managed KMS keys for enhanced control over encryption keys with rotation policies.
- Use IAM Roles to authenticate access to DynamoDB
- Implement resource-based policies for simplified cross-account access control.
- Use Fine-Grained Access Control (FGAC) to control access at item and attribute level.
- Use VPC gateway endpoints for cost-effective private access from within VPC.
- Use interface endpoints (AWS PrivateLink) for private access from on-premises or cross-region.
- DynamoDB Encryption Client is a software library that helps in client-side encryption and protects the table data before you send it to DynamoDB.
- Enable AWS CloudTrail for auditing access to encryption keys and DynamoDB operations.
- Apply principle of least privilege when defining IAM policies.
- Regularly review and rotate access credentials and encryption keys.
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- What are the services supported by VPC endpoints, using the Gateway endpoint type?
- Amazon EFS
- Amazon DynamoDB
- Amazon Glacier
- Amazon SQS
- A company needs to provide cross-account access to a DynamoDB table without requiring IAM role assumption. Which feature should they use?
- IAM identity policies
- VPC endpoint policies
- Resource-based policies
- Fine-grained access control
- A company needs to access DynamoDB from their on-premises data center over AWS Direct Connect without traversing the public internet. Which solution should they use?
- VPC gateway endpoint
- VPC interface endpoint with AWS PrivateLink
- Internet gateway
- NAT gateway
- Which DynamoDB Streams access method supports AWS PrivateLink?
- Gateway endpoints
- Interface endpoints
- Both gateway and interface endpoints
- Neither gateway nor interface endpoints
- A company wants to minimize costs for private VPC access to DynamoDB from EC2 instances within the same VPC. Which endpoint type should they use?
- Interface endpoint
- Gateway endpoint
- Both are equally cost-effective
- Neither supports this use case
- Which of the following statements about DynamoDB security are correct? (Select THREE)
- Resource-based policies simplify cross-account access
- Gateway endpoints are accessible from on-premises networks
- DAX supports AWS PrivateLink for management APIs
- Encryption at rest can be disabled for tables
- DynamoDB Streams only supports interface endpoints, not gateway endpoints
- What encryption key type provides the most control over key management for DynamoDB?
- AWS owned key
- AWS managed key
- Customer managed key
- All provide equal control
2 thoughts on “AWS DynamoDB Security”
Comments are closed.