AWS Network Firewall
- AWS Network Firewall is stateful, fully managed, network firewall and intrusion detection and prevention service (IDS/IPS) for VPCs.
- Network Firewall scales automatically with the network traffic, without the need for deploying and managing any infrastructure.
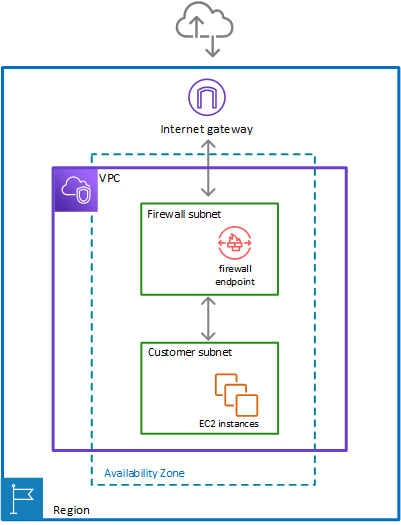
- AWS Network Firewall
- can filter traffic at the perimeter of the VPC. This includes filtering traffic going to and coming from an internet gateway, NAT gateway, or over VPN or AWS Direct Connect.
- protects the subnets within the VPC by filtering traffic going between the subnets and locations outside of the VPC
- flexible rules engine allows defining firewall rules that give fine-grained control over network traffic, such as blocking outbound Server Message Block (SMB) requests to prevent the spread of malicious activity.
- supports importing rules already written in common open source rule formats as well as enables integrations with managed intelligence feeds sourced by AWS partners.
- works together with AWS Firewall Manager to build policies based on AWS Network Firewall rules and then centrally apply those policies across the VPCs and accounts.
- helps provide protection from common network threats.
- can incorporate context from traffic flows, like tracking connections and protocol identification, to enforce policies such as preventing the VPCs from accessing domains using an unauthorized protocol.
- supports intrusion prevention system (IPS) to provide active traffic flow inspection to help identify and block vulnerability exploits using signature-based detection.
- uses the open source intrusion prevention system (IPS), Suricata, for stateful inspection and supports Suricata compatible rules.
- supports web filtering that can stop traffic to known bad URLs and monitor fully qualified domain names.
AWS Network Firewall Latest Features (2024-2026)
TLS Inspection (Advanced Inspection)
- AWS Network Firewall now supports TLS inspection capabilities through Advanced Inspection feature.
- Enables decryption and re-encryption of HTTPS traffic for deep packet inspection of encrypted data.
- Helps mitigate filter bypass attempts and identify security risks in encrypted traffic.
- Supports both inbound and outbound TLS inspection configurations.
- Requires ACM certificates for inbound traffic and ACM Private CA for outbound traffic.
- Pricing Update (February 2026): AWS removed additional data processing charges for Advanced Inspection, making TLS inspection more cost-effective.
Web Category-Based Filtering (January 2026)
- New capability for URL and Domain Category filtering using predefined content categories.
- Enables identification and control of access to:
- Generative AI (GenAI) services
- Social media platforms
- Streaming sites
- Other web categories
- Simplifies governance and compliance by allowing category-based rules instead of maintaining extensive URL lists.
- Works with Suricata compatible rule strings and standard Network Firewall stateful rule groups.
- When combined with TLS inspection, provides granular control over full URL path inspection.
Enhanced Integration with VPC Lattice
- AWS Network Firewall now works in combination with Amazon VPC Lattice for comprehensive security architecture.
- VPC Lattice provides identity-based access controls for HTTP/HTTPS service-to-service communication.
- Combined approach allows:
- Deep packet inspection via Network Firewall for traffic requiring malware detection and IPS/IDS
- Identity-based routing via VPC Lattice for HTTP/HTTPS communications
- Cost optimization by reducing Network Firewall processing for non-critical traffic
Pricing Improvements (February 2026)
- NAT Gateway Discounts Extended: Hourly and data processing discounts now apply to both primary and secondary Network Firewall endpoints when service-chained with NAT Gateways.
- Advanced Inspection Cost Reduction: Removed additional data processing charges ($0.001/GB to $0.009/GB) for TLS inspection in 13 AWS regions.
- Multiple VPC Endpoint Support: Connect up to 50 VPCs per Availability Zone to a single Network Firewall, reducing operational complexity and costs.
AWS Network Firewall Components
- Rule Group
- Holds a reusable collection of criteria for inspecting traffic and for handling packets and traffic flows that match the inspection criteria.
- Rule groups are either stateless or stateful.
- Rules configuration includes 5-tuple and domain name filtering.
- Enhanced with URL Category Filtering: Now supports predefined web categories for simplified governance.
- Firewall policy
- Defines a reusable set of stateless and stateful rule groups, along with some policy-level behaviour settings.
- Firewall policy provides the network traffic filtering behaviour for a firewall.
- A single firewall policy can be used in multiple firewalls.
- TLS Inspection Configuration: Can include Advanced Inspection settings for encrypted traffic analysis.
- Firewall
- Connects the inspection rules in the firewall policy to the VPC that the rules protect.
- Each firewall requires one firewall policy.
- The firewall additionally defines settings like how to log information about the network traffic and the firewall’s stateful traffic filtering.
- Multiple VPC Endpoints: Supports connecting multiple VPCs (up to 50 per AZ) to a single firewall instance.
Stateless and Stateful Rules Engines
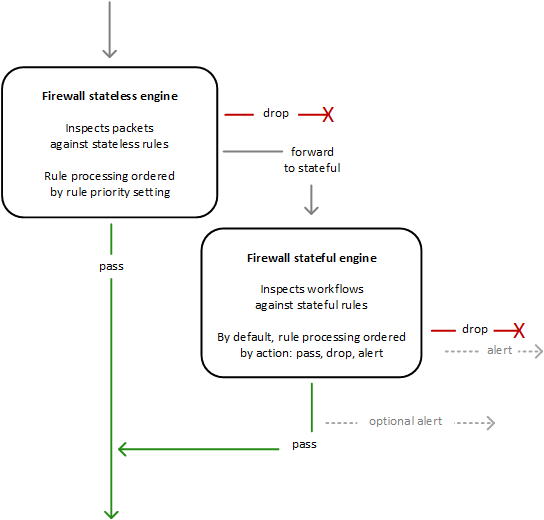
- AWS Network Firewall uses two rules engines to inspect packets according to the rules that you provide in your firewall policy.
- Stateless Rules Engine
- First, the Stateless engine inspects the packet against the configured stateless rules.
- Each packet inspection happens in isolation, without regard to factors such as the direction of traffic, or whether the packet is part of an existing, approved connection.
- This engine prioritizes the speed of evaluation and it takes rules with standard 5-tuple connection criteria.
- The engine processes the rules in the defined priority order and stops processing when it finds a match.
- Network Firewall stateless rules are similar in behaviour and use to VPC network access control lists (ACLs).
- Depending on the packet settings, the stateless inspection criteria, and the firewall policy settings, the stateless engine might
- drop a packet,
- pass it through to its destination, or
- forward it to the stateful rules engine.
- Stateful Rules Engine
- Stateful engine inspects packets in the context of their traffic flow, using the configured stateful rules.
- Packets are inspected in the context of their traffic flow.
- Stateful rules consider traffic direction. The stateful rules engine might delay packet delivery in order to group packets for inspection.
- By default, the stateful rules engine processes the rules in the order of their action setting, with pass rules processed first, then drop, and then alert. The engine stops processing when it finds a match.
- The stateful engine either
- drops packets or
- passes them to their destination.
- Stateful engine activities send flow and alert logs to the firewall’s logs if logging is configured.
- Stateful engine sends alerts for dropped packets and can optionally send them for passed packets.
- Stateful rules are similar in behaviour and use to VPC security groups.
- By default, the stateful rules engine allows traffic to pass, while the security groups default is to deny traffic.
- Enhanced with TLS Inspection: Can now decrypt and inspect encrypted traffic when Advanced Inspection is enabled.
- URL Category Support: Supports filtering based on predefined web categories for improved governance.
AWS Network Firewall Use Cases and Best Practices
Modern Deployment Patterns
- Hybrid Security Architecture: Combine Network Firewall with VPC Lattice for optimal security and cost efficiency.
- Centralized Inspection: Use for traffic requiring deep packet inspection, malware detection, and IPS/IDS capabilities.
- GenAI Governance: Implement category-based filtering to control access to AI services and ensure compliance.
- Educational Institutions: Web filtering with TLS inspection for comprehensive content control.
- Multi-VPC Architectures: Leverage multiple VPC endpoint capability to protect up to 50 VPCs per AZ cost-effectively.
Integration with AWS Services
- AWS Transit Gateway: Simplified integration for centralized inspection architectures.
- AWS Cloud WAN: Service insertion capabilities for global security inspection.
- AWS Firewall Manager: Centralized policy management across multiple accounts and VPCs.
- Amazon VPC Lattice: Combined approach for service-to-service communication security.
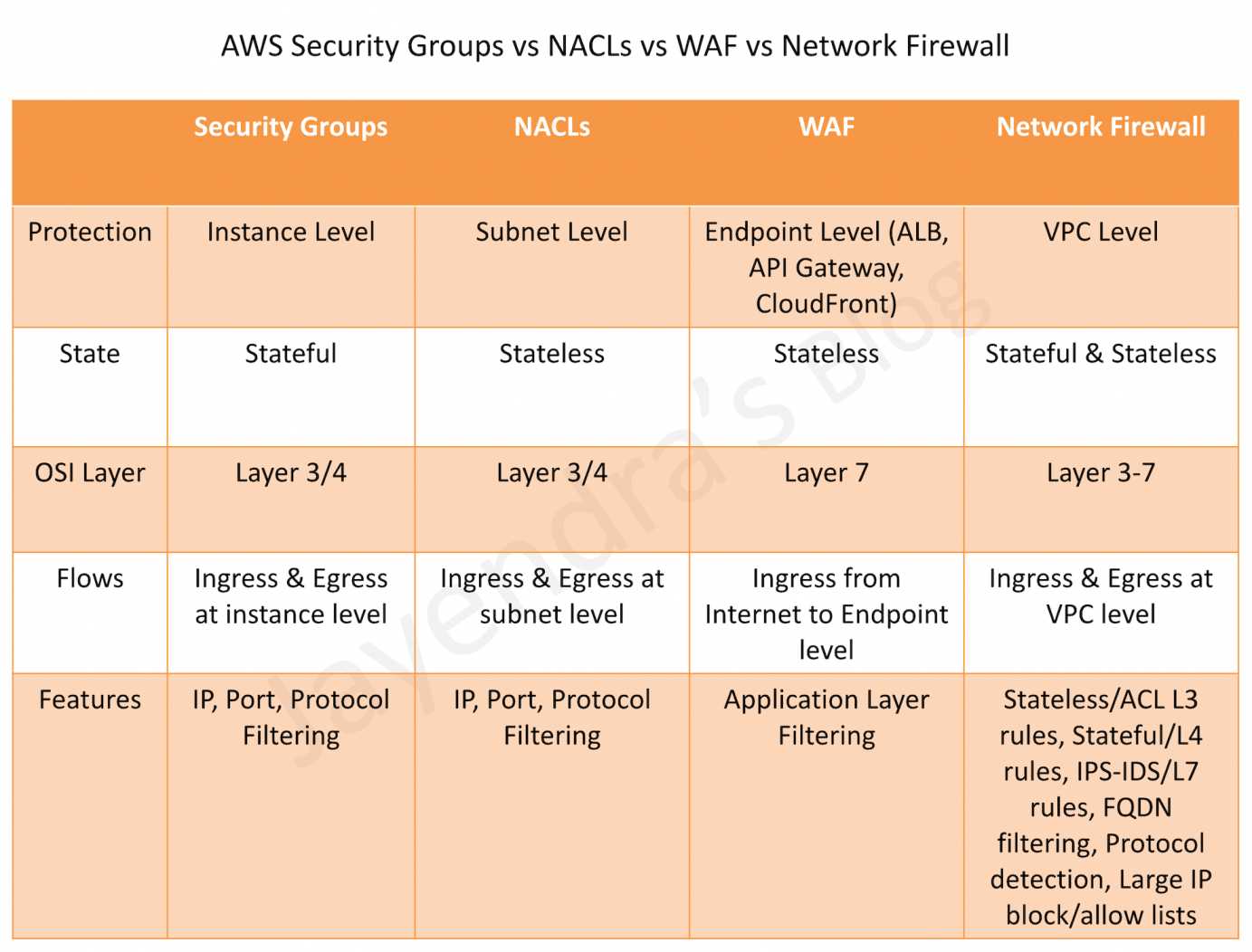
AWS Network Firewall vs WAF vs Security Groups vs NACLs
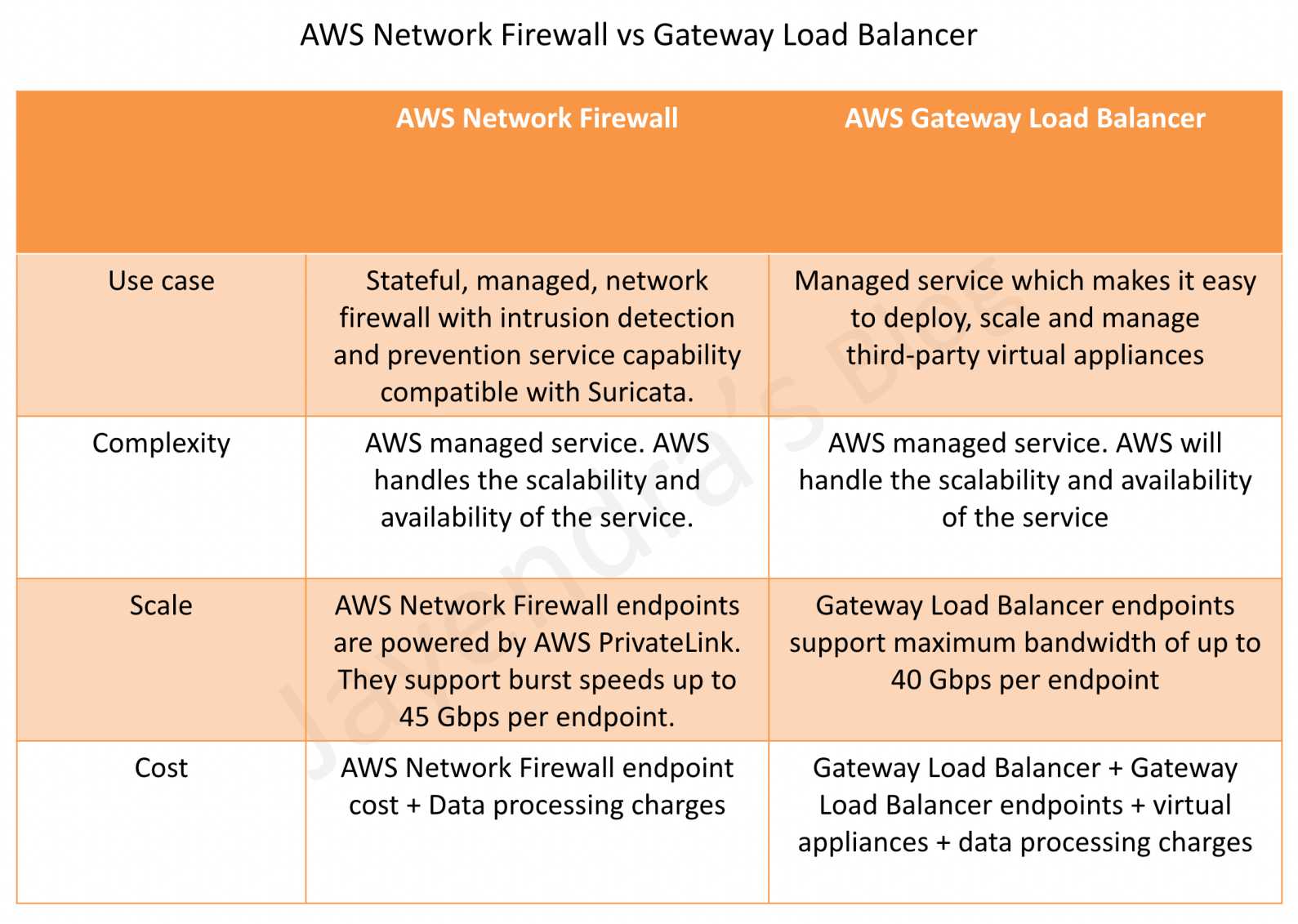
AWS Network Firewall vs Gateway Load Balancer
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- A company needs to inspect encrypted HTTPS traffic for malware detection in their VPC. Which AWS Network Firewall feature should they implement?
- A. Stateful rule groups with domain filtering
- B. Advanced Inspection with TLS inspection
- C. Stateless rules with 5-tuple matching
- D. URL category filtering
Answer: B
Advanced Inspection with TLS inspection enables decryption and re-encryption of HTTPS traffic for deep packet inspection of encrypted data, allowing malware detection in encrypted traffic. - An organization wants to block access to social media and streaming platforms across their AWS environment. Which Network Firewall feature provides the most efficient solution?
- A. Creating individual domain-based stateful rules for each platform
- B. Using URL category-based filtering with predefined categories
- C. Implementing custom Suricata rules for each service
- D. Configuring stateless rules with IP address ranges
Answer: B
URL category-based filtering allows blocking entire categories like social media and streaming platforms using predefined categories, which is more efficient than maintaining individual rules. - A company has 40 VPCs that need firewall protection. What is the most cost-effective approach using AWS Network Firewall?
- A. Deploy a separate Network Firewall in each VPC
- B. Use a single Network Firewall with multiple VPC endpoints (up to 50 per AZ)
- C. Implement AWS WAF for all VPCs
- D. Use VPC security groups only
Answer: B
Network Firewall supports connecting up to 50 VPCs per Availability Zone to a single firewall instance, reducing operational complexity and costs compared to individual firewalls. - Which combination provides the most comprehensive and cost-effective security architecture for service-to-service communication?
- A. AWS Network Firewall only for all traffic
- B. Amazon VPC Lattice only for all communications
- C. AWS Network Firewall for deep packet inspection and VPC Lattice for HTTP/HTTPS identity-based controls
- D. AWS WAF and Application Load Balancer
Answer: C
The combined approach uses Network Firewall for traffic requiring deep packet inspection and VPC Lattice for HTTP/HTTPS service communications with identity-based controls, optimizing both security and cost. - A financial institution needs to control access to GenAI services while maintaining compliance. Which AWS Network Firewall feature is most appropriate?
- A. Stateless rules with port-based filtering
- B. Traditional domain-based stateful rules
- C. URL category filtering with GenAI category controls
- D. IPS/IDS signature-based detection only
Answer: C
URL category filtering includes predefined GenAI categories, allowing institutions to easily control access to AI services while meeting compliance requirements.