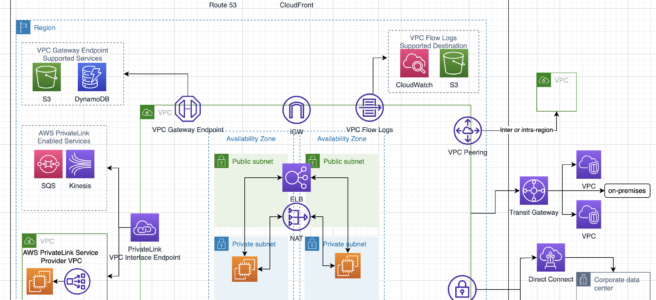
VPC Peering
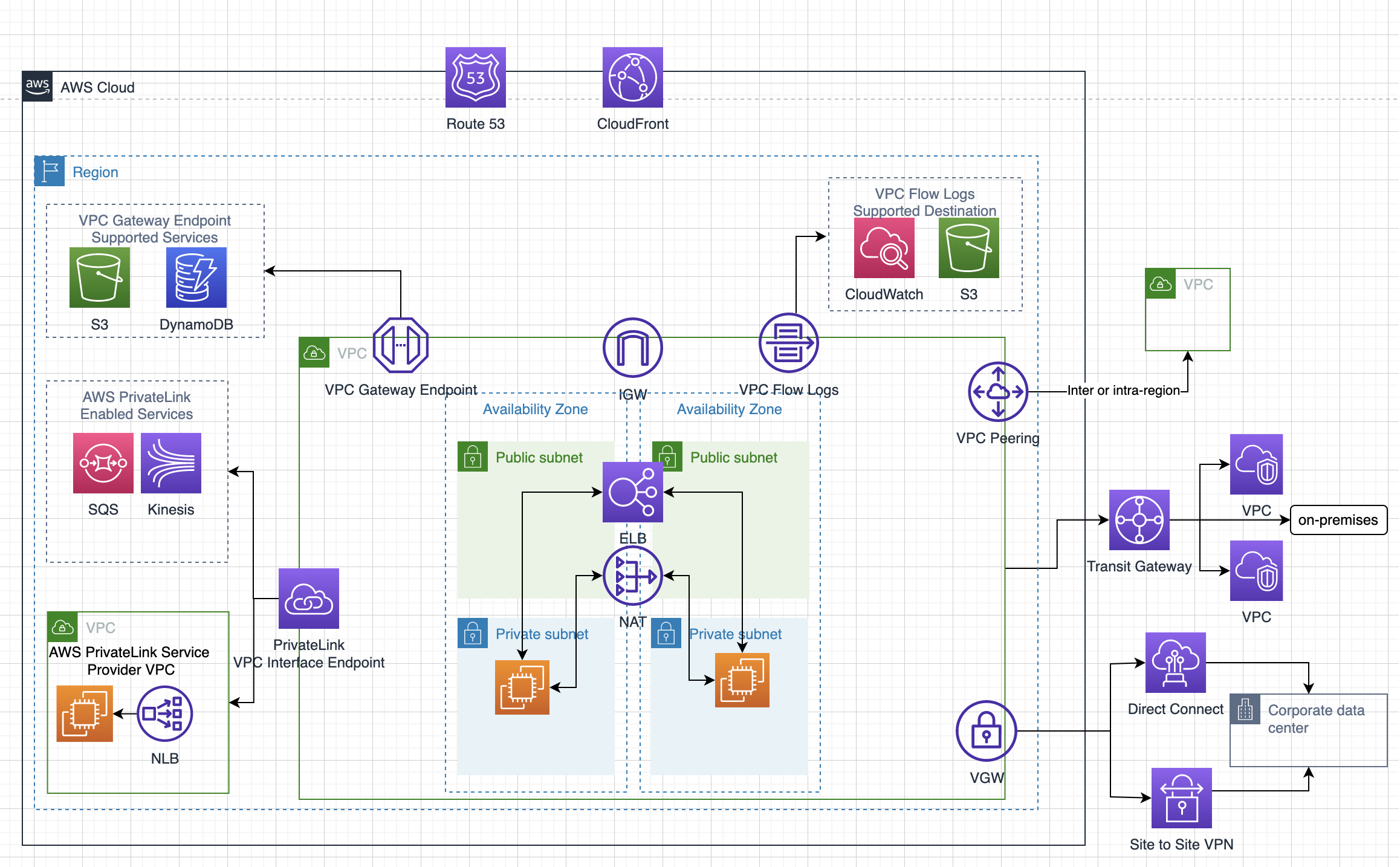
- A VPC peering connection is a networking connection between two VPCs that enables routing of traffic between them using private IPv4 addresses or IPv6 addresses.
- VPC peering connection
- can be established between your own VPCs, or with a VPC in another AWS account in the same or different region.
- is a one-to-one relationship between two VPCs.
- supports intra and inter-region peering connections.
- With VPC peering,
- Instances in either VPC can communicate with each other as if they are within the same network
- AWS uses the existing infrastructure of a VPC to create a peering connection; it is neither a gateway nor a VPN connection and does not rely on a separate piece of physical hardware.
- There is no single point of failure for communication or a bandwidth bottleneck
- All inter-region traffic is encrypted with no single point of failure, or bandwidth bottleneck. Traffic always stays on the global AWS backbone, and never traverses the public internet, which reduces threats, such as common exploits, and DDoS attacks.
- VPC peering pricing
- There is no charge to create a VPC peering connection.
- All data transfer over a VPC peering connection that stays within an Availability Zone is free, even if it’s between different accounts.
- Charges apply for data transfer over VPC peering connections that cross Availability Zones and Regions.
VPC Peering Connectivity
- To create a VPC peering connection, the owner of the requester VPC sends a request to the owner of the accepted VPC.
- Accepter VPC can be owned by the same account or a different AWS account.
- Once the Accepter VPC accepts the peering connection request, the peering connection is activated.
- Route tables on both the VPCs should be manually updated to allow traffic
- Security groups on the instances should allow traffic to and from the peered VPCs.
VPC Peering Limitations & Rules
- Does not support Overlapping or matching IPv4 or IPv6 CIDR blocks.
- Does not support transitive peering relationships i.e. the VPC does not have access to any other VPCs that the peer VPC may be peered with even if established entirely within your own AWS account
- Does not support Edge to Edge Routing Through a Gateway or Private Connection
- In a VPC peering connection, the VPC does not have access to any other connection that the peer VPC may have and vice versa. Connections that the peer VPC can include
- A VPN connection or an AWS Direct Connect connection to a corporate network
- An Internet connection through an Internet gateway
- An Internet connection in a private subnet through a NAT device
- A VPC endpoint to an AWS service; for example, an endpoint to S3.
- VPC peering connections quotas
- Default limit of 50 active VPC peering connections per VPC, which can be increased up to a maximum of 125.
- Default limit of 25 outstanding VPC peering connection requests.
- Unaccepted VPC peering connection requests expire after 1 week (168 hours).
- Only one peering connection can be established between the same two VPCs at the same time.
- Jumbo frames are supported for peering connections within the same region.
- A placement group can span peered VPCs that are in the same region; however, you do not get full-bisection bandwidth between instances in peered VPCs
- Inter-region VPC peering connections
- The Maximum Transmission Unit (MTU) across an inter-region peering connection is 1500 bytes. Jumbo frames are not supported.
- Security group rule that references a peer VPC security group cannot be created.
- Any tags created for the peering connection are only applied in the account or region in which they were created
- Unicast reverse path forwarding in peering connections is not supported
- Instance’s Public DNS can be resolved to its private IP address across peered VPCs when DNS resolution is enabled for the VPC peering connection.
⚠️ DEPRECATED FEATURE
EC2-Classic and ClassicLink were retired on August 15, 2023.
The original content mentioned ClassicLink connections to EC2-Classic instances. This feature is no longer available.
Migration: All resources must be migrated to VPC. EC2-Classic is no longer supported.
VPC Peering Troubleshooting
- Verify that the VPC peering connection is in the Active state.
- Be sure to update the route tables for the peering connection. Verify that the correct routes exist for connections to the IP address range of the peered VPCs through the appropriate gateway.
- Verify that an ALLOW rule exists in the network access control (NACL) table for the required traffic.
- Verify that the security group rules allow network traffic between the peered VPCs.
- Verify using VPC flow logs that the required traffic isn’t rejected at the source or destination. This rejection might occur due to the permissions associated with security groups or network ACLs.
- Be sure that no firewall rules block network traffic between the peered VPCs. Use network utilities such as
traceroute(Linux) ortracert(Windows) to check rules for firewalls such as iptables (Linux) or Windows Firewall (Windows). - For DNS resolution issues, ensure that DNS resolution is enabled for the VPC peering connection to resolve public DNS hostnames to private IP addresses.
VPC Peering Architecture

- VPC Peering can be applied to create shared services or perform authentication with an on-premises instance
- This would help create a single point of contact, as well limiting the VPN connections to a single account or VPC
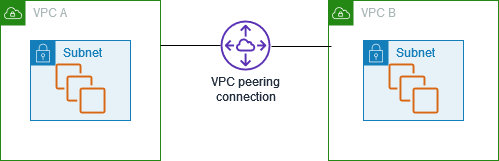
VPC Peering vs Transit Gateway vs PrivateLink
When to Use Each Solution
- VPC Peering
- Best for: Simple, direct connections between a small number of VPCs (typically less than 10)
- Advantages: No additional cost for the connection itself, low latency, simple setup
- Limitations: Does not support transitive routing, becomes complex at scale (mesh topology), limited to 125 peering connections per VPC
- AWS Transit Gateway
- Best for: Hub-and-spoke architecture with many VPCs (10+), centralized routing, hybrid connectivity
- Advantages: Supports transitive routing, centralized management, scales to thousands of VPCs, integrates with Direct Connect and VPN
- Limitations: Additional cost per attachment and data processing, slightly higher latency than direct peering
- AWS PrivateLink
- Best for: Service-to-service connectivity, exposing services to multiple consumers, SaaS applications
- Advantages: Unidirectional access, no VPC CIDR overlap issues, enhanced security, supports cross-account and cross-region access
- Limitations: Requires Network Load Balancer or Gateway Load Balancer, additional cost, one-way communication by default
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- You currently have 2 development environments hosted in 2 different VPCs in an AWS account in the same region. There is now a need for resources from one VPC to access another. How can this be accomplished?
- Establish a Direct Connect connection.
- Establish a VPN connection.
- Establish VPC Peering.
- Establish Subnet Peering.
- A company has an AWS account that contains three VPCs (Dev, Test, and Prod) in the same region. Test is peered to both Prod and Dev. All VPCs have non-overlapping CIDR blocks. The company wants to push minor code releases from Dev to Prod to speed up the time to market. Which of the following options helps the company accomplish this?
- Create a new peering connection Between Prod and Dev along with appropriate routes.
- Create a new entry to Prod in the Dev route table using the peering connection as the target.
- Attach a second gateway to Dev. Add a new entry in the Prod route table identifying the gateway as the target.
- The VPCs have non-overlapping CIDR blocks in the same account. The route tables contain local routes for all VPCs.
- A company has 2 AWS accounts that have individual VPCs. The VPCs are in different AWS regions and need to communicate with each other. The VPCs have non-overlapping CIDR blocks. Which of the following would be a cost-effective connectivity option?
- Use VPN connections
- Use VPC peering between the 2 VPC’s
- Use AWS Direct Connect
- Use a NAT gateway
- A company needs to connect 15 VPCs across multiple AWS accounts and regions with centralized routing and management. Which solution is most appropriate?
- Create VPC peering connections between all VPCs
- Use AWS Transit Gateway with a hub-and-spoke architecture
- Use AWS PrivateLink for all connections
- Use multiple VPN connections
- A SaaS provider wants to expose their application running in their VPC to multiple customer VPCs without requiring VPC peering or overlapping CIDR concerns. Which solution should they use?
- VPC Peering with each customer VPC
- AWS Transit Gateway
- AWS PrivateLink with VPC endpoint service
- Internet Gateway with security groups