AWS VPC – Virtual Private Cloud
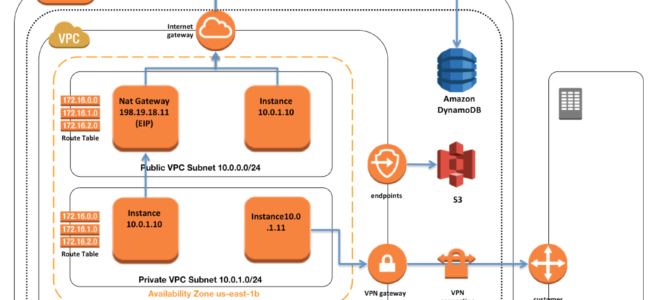
- AWS VPC – Virtual Private Cloud is a virtual network dedicated to the AWS account. It is logically isolated from other virtual networks in the AWS cloud.
- VPC allows the users complete control over their virtual networking environment, including the selection of their own IP address range, creation of subnets, and configuration of route tables and network gateways.
- VPC allows you to use both IPv4 and IPv6 in your VPC for secure and easy access to resources and applications.
- VPC is a regional service and it spans all of the AZs in the Region. Availability zones (AZ) are multiple, isolated locations within each Region.
- VPC Sizing
- VPC needs a set of IP addresses in the form of a Classless Inter-Domain Routing (CIDR) block for e.g, 10.0.0.0/16, which allows 2^16 (65536) IP address to be available
- Allowed CIDR block size is between
- /28 netmask (minimum with 2^4 – 16 available IP address) and
- /16 netmask (maximum with 2^16 – 65536 IP address)
- CIDR block from private (non-publicly routable) IP address can be assigned
- 10.0.0.0 – 10.255.255.255 (10/8 prefix)
- 172.16.0.0 – 172.31.255.255 (172.16/12 prefix)
- 192.168.0.0 – 192.168.255.255 (192.168/16 prefix)
- It’s possible to specify a range of publicly routable IP addresses; however, direct access to the Internet is not currently supported from publicly routable CIDR blocks in a VPC
CIDR block once assigned to the VPC cannot be modified.NOTE – You can now resize VPC. Read AWS blog post.- Each VPC is separate from any other VPC created with the same CIDR block even if it resides within the same AWS account
- Connection between your VPC and corporate or home network can be established, however, the CIDR blocks should be not be overlapping for e.g. VPC with CIDR 10.0.0.0/16 can communicate with 10.1.0.0/16 corporate network but the connections would be dropped if it tries to connect to 10.0.37.0/16 corporate network cause of overlapping IP addresses.
- VPC allows you to set tenancy options for the Instances launched in it. By default, the tenancy option is shared. If the dedicated option is selected, all the instances within it are launched on dedicated hardware overriding the individual instance tenancy setting.
- Deletion of the VPC is possible only after terminating all instances within the VPC and deleting all the components with the VPC e.g. subnets, security groups, network ACLs, route tables, Internet gateways, VPC peering connections, and DHCP options
- VPC Peering provides a networking connection between two VPCs (same or different account and region) that enables routing of traffic between them using private IPv4 addresses or IPv6 addresses.
- NAT Gateway enables instances in a private subnet to connect to the Internet but prevents the Internet from initiating connections with the instances.
- VPC endpoints enable the creation of a private connection between VPC to supported AWS services and VPC endpoint services powered by PrivateLink using its private IP address.
Subnets
- Subnet spans a single Availability Zone, distinct locations engineered to be isolated from failures in other AZs, and cannot span across AZs
- Subnet can be configured with an Internet gateway to enable communication over the Internet, or virtual private gateway (VPN) connection to enable communication with your corporate network
- Subnet can be Public or Private and it depends on whether it has Internet connectivity i.e. is able to route traffic to the Internet through the IGW
- Instances within the Public Subnet should be assigned a Public IP or Elastic IP address to be able to communicate with the Internet
- For Subnets not connected to the Internet, but has traffic routed through Virtual Private Gateway only is termed as VPN-only subnet
- Subnets can be configured to Enable assignment of the Public IP address to all the Instances launched within the Subnet by default, which can be overridden during the creation of the Instance
- Subnet Sizing
- CIDR block assigned to the Subnet can be the same as the VPC CIDR, in this case you can launch only one subnet within your VPC
- CIDR block assigned to the Subnet can be a subset of the VPC CIDR, which allows you to launch multiple subnets within the VPC
- CIDR block assigned to the subnet should not be overlapping
- CIDR block size allowed is between
- /28 netmask (minimum with 2^4 – 16 available IP address) and
- /16 netmask (maximum with 2^16 – 65536 IP address)
- AWS reserves 5 IPs address (first 4 and last 1 IP address) in each Subnet which are not available for use and cannot be assigned to an instance. for e.g. for a Subnet with a CIDR block 10.0.0.0/24 the following five IPs are reserved
- 10.0.0.0: Network address
- 10.0.0.1: Reserved by AWS for the VPC router
- 10.0.0.2: Reserved by AWS for mapping to Amazon-provided DNS
- 10.0.0.3: Reserved by AWS for future use
- 10.0.0.255: Network broadcast address. AWS does not support broadcast in a VPC, therefore the address is reserved.
- Subnet Routing
- Each Subnet is associated with a route table that controls the traffic.
- Subnet Security
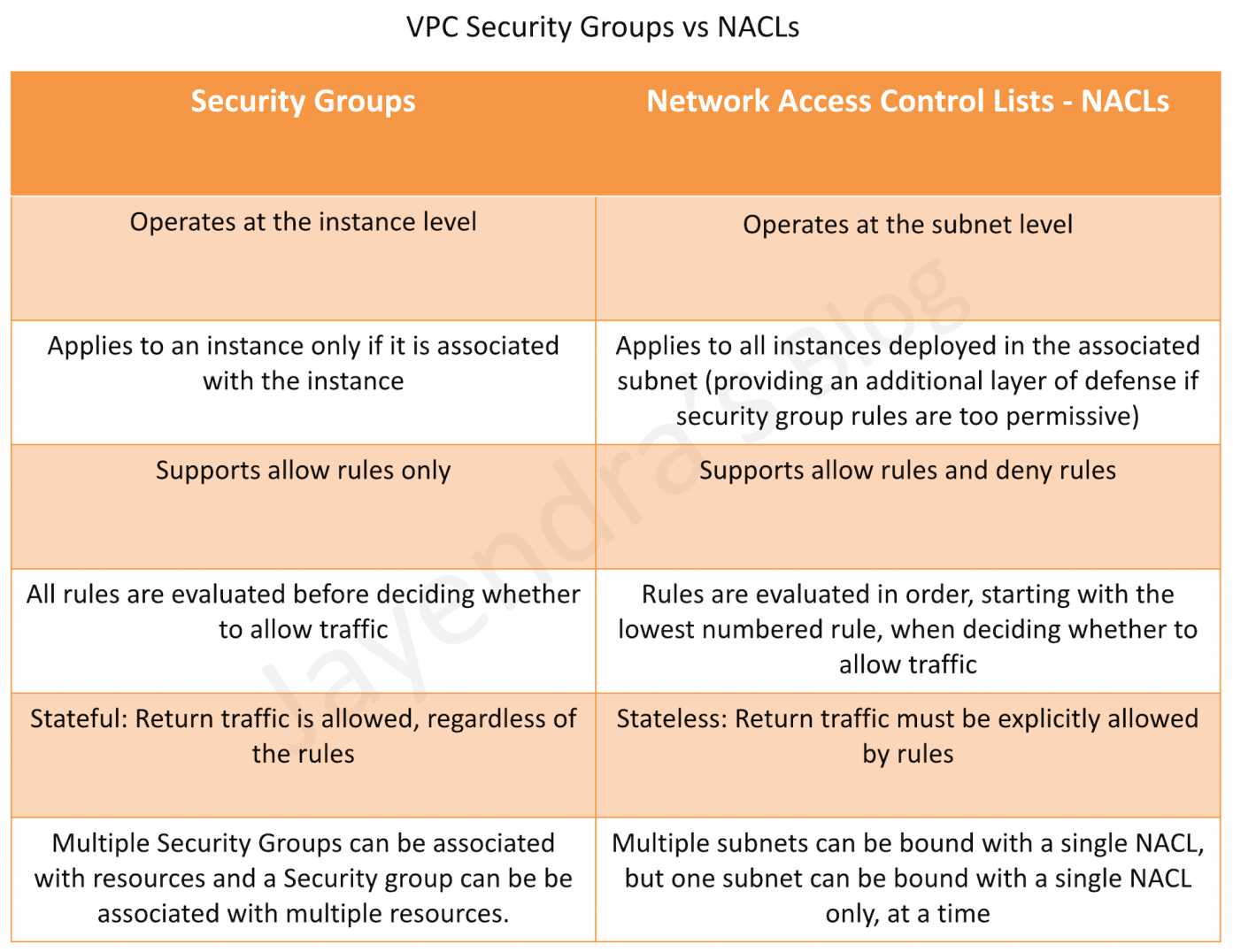
- Subnet security can be configured using Security groups and NACLs
- Security groups work at the instance level, and NACLs work at the subnet level
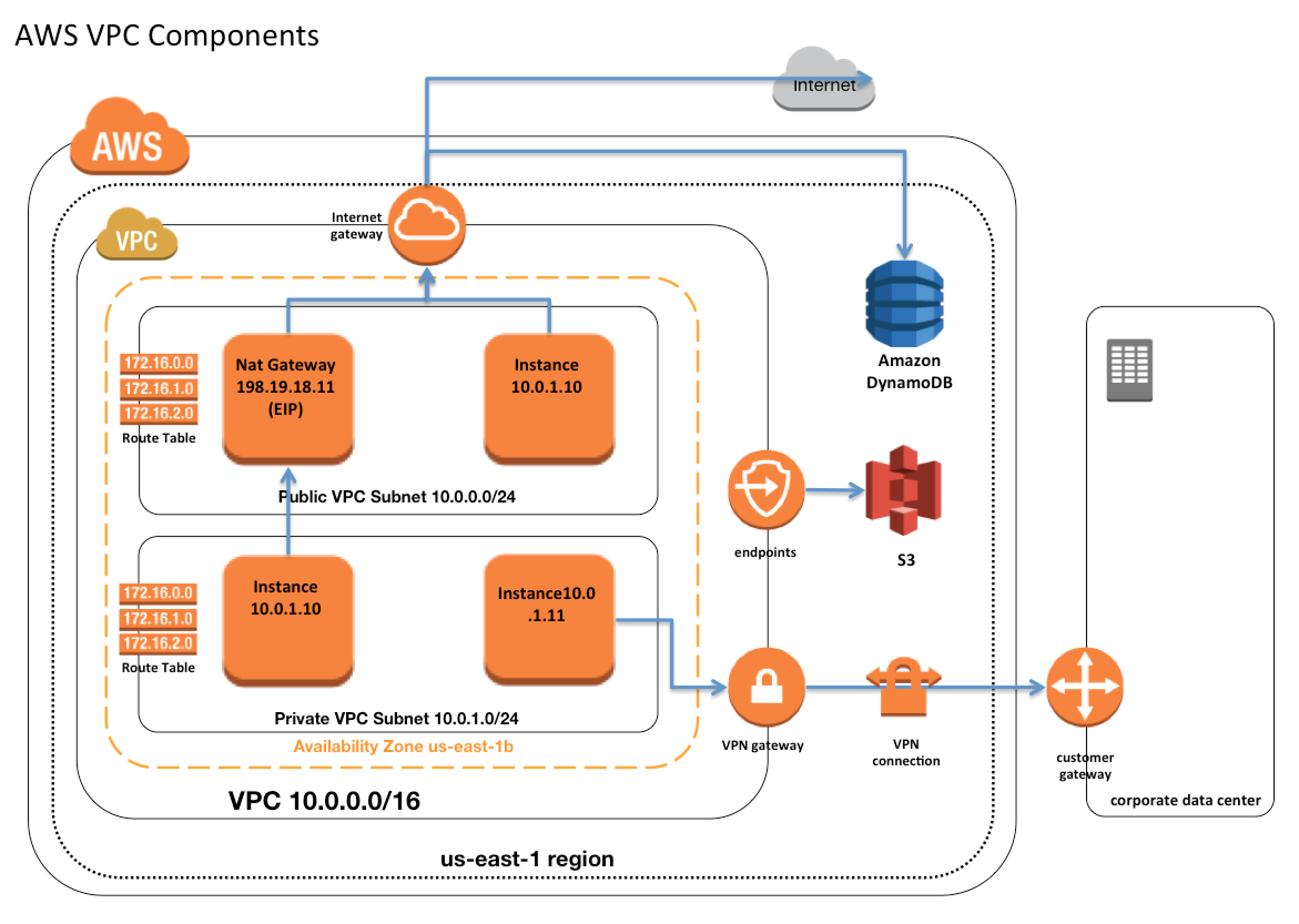
VPC & Subnet Sizing
- VPC supports IPv4 and IPv6 addressing and has different CIDR block size limits for each
- IPv6 CIDR block can be optionally associated with the VPC
- VPC IPv4 CIDR block cannot be modified once created i.e. cannot increase or decrease the size of an existing CIDR block.
- However, secondary CIDR blocks can be associated with the VPC to extend the VPC
- Limitations
- allowed block size is between a
/28netmask and/16netmask. - CIDR block must not overlap with any existing CIDR block that’s associated with the VPC.
- CIDR block must not be the same or larger than the CIDR range of a route in any of the VPC route tables for e.g. for a CIDR block 10.0.0.0/24, can only associate smaller CIDR blocks like 10.0.0.0/25
- allowed block size is between a
IP Addresses
Instances launched in the VPC can have Private, Public, and Elastic IP addresses assigned to them and are properties of ENI (Network Interfaces)
- Private IP Addresses
- Private IP addresses are not reachable over the Internet, and can be used for communication only between the instances within the VPC
- All instances are assigned a private IP address, within the IP address range of the subnet, to the default network interface
- Primary IP address is associated with the network interface for its lifetime, even when the instance is stopped and restarted and is released only when the instance is terminated
- Additional Private IP addresses, known as secondary private IP address, can be assigned to the instances and these can be reassigned from one network interface to another
- Public IP address
- Public IP addresses are reachable over the Internet, and can be used for communication between instances and the Internet, or with other AWS services that have public endpoints
- Public IP address assignment to the Instance depends if the Public IP Addressing is enabled for the Subnet.
- Public IP address can also be assigned to the Instance by enabling the Public IP addressing during the creation of the instance, which overrides the subnet’s public IP addressing attribute
- Public IP address is assigned from AWS pool of IP addresses and it is not associated with the AWS account and hence is released when the instance is stopped and restarted or terminated.
- Elastic IP address
- Elastic IP addresses are static, persistent public IP addresses that can be associated and disassociated with the instance, as required
- Elastic IP address is allocated to the VPC and owned by the account unless released.
- A Network Interface can be assigned either a Public IP or an Elastic IP. If you assign an instance, that already has a Public IP, an Elastic IP, the public IP is released
- Elastic IP addresses can be moved from one instance to another, which can be within the same or different VPC within the same account
- Elastic IPs are charged for non-usage i.e. if it is not associated or associated with a stopped instance or an unattached Network Interface
Elastic Network Interface (ENI)
- Each Instance is attached to a default elastic network interface (Primary Network Interface eth0) and cannot be detached from the instance
- ENI can include the following attributes
- Primary private IP address
- One or more secondary private IP addresses
- One Elastic IP address per private IP address
- One public IP address, which can be auto-assigned to the network interface for eth0 when you launch an instance, but only when you create a network interface for eth0 instead of using an existing ENI
- One or more security groups
- A MAC address
- A source/destination check flag
- A description
- ENI’s attributes follow the ENI as it is attached or detached from an instance and reattached to another instance. When an ENI is moved from one instance to another, network traffic is redirected to the new instance.
- Multiple ENIs can be attached to an instance and is useful for use cases:
- Create a management network.
- Use network and security appliances in your VPC.
- Create dual-homed instances with workloads/roles on distinct subnets.
- Create a low-budget, high-availability solution.
Route Tables
- Route table defines rules, termed as routes, which determine where network traffic from the subnet would be routed
- Each VPC has an implicit router to route network traffic
- Each VPC has a Main Route table and can have multiple custom route tables created
- Each Subnet within a VPC must be associated with a single route table at a time, while a route table can have multiple subnets associated with it
- Subnet, if not explicitly associated to a route table, is implicitly associated with the main route table
- Every route table contains a local route that enables communication within a VPC which cannot be modified or deleted
- Route priority is decided by matching the most specific route in the route table that matches the traffic
- Route tables need to be updated to define routes for Internet gateways, Virtual Private gateways, VPC Peering, VPC Endpoints, NAT Devices, etc.
Internet Gateways – IGW
- An Internet gateway is a horizontally scaled, redundant, and highly available VPC component that allows communication between instances in the VPC and the Internet.
- IGW imposes no availability risks or bandwidth constraints on the network traffic.
- An Internet gateway serves two purposes:
- To provide a target in the VPC route tables for Internet-routable traffic,
- To perform network address translation (NAT) for instances that have been NOT been assigned public IP addresses.
- Enabling Internet access to an Instance requires
- Attaching Internet gateway to the VPC
- Subnet should have route tables associated with the route pointing to the Internet gateway
- Instances should have a Public IP or Elastic IP address assigned
- Security groups and NACLs associated with the Instance should allow relevant traffic
NAT
- NAT device enables instances in a private subnet to connect to the Internet or other AWS services, but prevents the Internet from initiating connections with the instances.
- NAT devices do not support IPv6 traffic, use an egress-only Internet gateway instead.
Refer to My Blog Post about VPC NAT
Egress-only Internet gateway
- Egress-only Internet gateway works as a NAT gateway, but for IPv6 traffic
- Egress-only Internet gateway is a horizontally scaled, redundant, and highly available VPC component that allows outbound communication over IPv6 from instances in the VPC to the Internet, and prevents the Internet from initiating an IPv6 connection with the instances.
- An egress-only Internet gateway is for use with IPv6 traffic only. To enable outbound-only Internet communication over IPv4, use a NAT gateway instead.
Shared VPCs
- VPC sharing allows multiple AWS accounts to create their application resources, such as EC2 instances, RDS databases, Redshift clusters, and AWS Lambda functions, into shared, centrally-managed VPCs.
- In this model, the account that owns the VPC (owner) shares one or more subnets with other accounts (participants) that belong to the same organization from AWS Organizations.
- After a subnet is shared, the participants can view, create, modify, and delete their application resources in the subnets shared with them. Participants cannot view, modify, or delete resources that belong to other participants or the VPC owner.
VPC Endpoints
- VPC endpoint enables the creation of a private connection between VPC to supported AWS services and VPC endpoint services powered by PrivateLink using its private IP address
- Endpoints do not require a public IP address, access over the Internet, NAT device, a VPN connection, or AWS Direct Connect.
- Traffic between VPC and AWS service does not leave the Amazon network
- Endpoints are virtual devices, that are horizontally scaled, redundant, and highly available VPC components that allow communication between instances in the VPC and AWS services without imposing availability risks or bandwidth constraints on your network traffic.
- Endpoints currently do not support cross-region requests, ensure that the endpoint is created in the same region as the S3 bucket
- AWS currently supports the following types of Endpoints
Refer to My Blog Post about VPC Endpoint
VPC Peering
- A VPC peering connection is a networking connection between two VPCs that enables the routing of traffic between them using private IPv4 addresses or IPv6 addresses.
- VPC peering connection is a one-to-one relationship between two VPCs and can be established between your own VPCs, or with a VPC in another AWS account in the same or different region.
- VPC peering helps instances in either VPC can communicate with each other as if they are within the same network using AWS’s existing infrastructure of a VPC to create a peering connection; it is neither a gateway nor a VPN connection and does not rely on a separate piece of physical hardware.
- VPC peering does not have any separate charges. However, there are data transfer charges.
Refer to My Blog Post about VPC Peering
VPC VPN Connections
Refer to My Blog Post about AWS VPC VPN Connections
VPC Security
- In a VPC, both Security Groups and Network ACLs (NACLS) together help to build a layered network defense.
- Security groups – Act as a virtual firewall for associated instances, controlling both inbound and outbound traffic at the instance level
- Network access control lists (NACLs) – Act as a firewall for associated subnets, controlling both inbound and outbound traffic at the subnet level
Security Groups & NACLs
Refer to My Blog Post about AWS Security Group vs NACLs
VPC Flow logs
- VPC Flow Logs help capture information about the IP traffic going to and from network interfaces in the VPC and can help in monitoring the traffic or troubleshooting any connectivity issues.
- Flow log data can be published to CloudWatch Logs, S3, and Kinesis Data Firehose.
- Flow log can be created for the entire VPC, subnets, or each network interface. If enabled, for the entire VPC or subnet all the network interfaces within that resource are monitored.
- Flow log can be configured to capture the type of traffic (accepted traffic, rejected traffic, or all traffic).
- Flow logs do not capture real-time log streams for network interfaces.
- Flow log data is collected outside of the path of the network traffic, and therefore does not affect network throughput or latency.
- Flow logs can be created for network interfaces that are created by other AWS services; for e.g., ELB, RDS, ElastiCache, Redshift, and WorkSpaces.
- Flow logs do not capture the following traffic
- Traffic generated by instances when they contact the Amazon DNS server.
- Traffic generated by a Windows instance for Amazon Windows license activation.
- Traffic to and from 169.254.169.254 for instance metadata
- Traffic to and from 169.254.169.123 for the Amazon Time Sync Service.
- DHCP traffic.
- Mirrored traffic.
- Traffic to the reserved IP address for the default VPC router.
- Traffic between an endpoint network interface and a Network Load Balancer network interface.
- Troubleshooting traffic flow
- If ACCEPT followed by REJECT, inbound was accepted by Security Groups and ACLs. However, rejected by NACLs outbound
- If REJECT, inbound was either rejected by Security Groups OR NACLs.
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- You have a business-to-business web application running in a VPC consisting of an Elastic Load Balancer (ELB), web servers, application servers and a database. Your web application should only accept traffic from predefined customer IP addresses. Which two options meet this security requirement? Choose 2 answers
- Configure web server VPC security groups to allow traffic from your customers’ IPs (Web server is behind the ELB and customer IPs will never reach web servers)
- Configure your web servers to filter traffic based on the ELB’s “X-forwarded-for” header (get the customer IPs and create a custom filter to restrict access. Refer link)
- Configure ELB security groups to allow traffic from your customers’ IPs and deny all outbound traffic (ELB will see the customer IPs so can restrict access, deny all is basically have no rules in outbound traffic, implicit, and its stateful so would work)
- Configure a VPC NACL to allow web traffic from your customers’ IPs and deny all outbound traffic (NACL is stateless, deny all will not work)
- A user has created a VPC with public and private subnets using the VPC Wizard. The VPC has CIDR 20.0.0.0/16. The private subnet uses CIDR 20.0.0.0/24. Which of the below mentioned entries are required in the main route table to allow the instances in VPC to communicate with each other?
- Destination : 20.0.0.0/24 and Target : VPC
- Destination : 20.0.0.0/16 and Target : ALL
- Destination : 20.0.0.0/0 and Target : ALL
- Destination : 20.0.0.0/16 and Target : Local
- A user has created a VPC with two subnets: one public and one private. The user is planning to run the patch update for the instances in the private subnet. How can the instances in the private subnet connect to the internet?
- Use the internet gateway with a private IP
- Allow outbound traffic in the security group for port 80 to allow internet updates
- The private subnet can never connect to the internet
- Use NAT with an elastic IP
- A user has launched an EC2 instance and installed a website with the Apache webserver. The webserver is running but the user is not able to access the website from the Internet. What can be the possible reason for this failure?
- The security group of the instance is not configured properly.
- The instance is not configured with the proper key-pairs.
- The Apache website cannot be accessed from the Internet.
- Instance is not configured with an elastic IP.
- A user has created a VPC with public and private subnets using the VPC wizard. Which of the below mentioned statements is true in this scenario?
- AWS VPC will automatically create a NAT instance with the micro size
- VPC bounds the main route table with a private subnet and a custom route table with a public subnet
- User has to manually create a NAT instance
- VPC bounds the main route table with a public subnet and a custom route table with a private subnet
- A user has created a VPC with public and private subnets. The VPC has CIDR 20.0.0.0/16. The private subnet uses CIDR 20.0.1.0/24 and the public subnet uses CIDR 20.0.0.0/24. The user is planning to host a web server in the public subnet (port 80) and a DB server in the private subnet (port 3306). The user is configuring a security group of the NAT instance. Which of the below mentioned entries is not required for the NAT security group?
- For Inbound allow Source: 20.0.1.0/24 on port 80
- For Outbound allow Destination: 0.0.0.0/0 on port 80
- For Inbound allow Source: 20.0.0.0/24 on port 80
- For Outbound allow Destination: 0.0.0.0/0 on port 443
- A user has created a VPC with CIDR 20.0.0.0/24. The user has used all the IPs of CIDR and wants to increase the size of the VPC. The user has two subnets: public (20.0.0.0/25) and private (20.0.0.128/25). How can the user change the size of the VPC?
- The user can delete all the instances of the subnet. Change the size of the subnets to 20.0.0.0/32 and 20.0.1.0/32, respectively. Then the user can increase the size of the VPC using CLI
- It is not possible to change the size of the VPC once it has been created (NOTE – You can now increase the VPC size. Read Post)
- User can add a subnet with a higher range so that it will automatically increase the size of the VPC
- User can delete the subnets first and then modify the size of the VPC
- A user has created a VPC with the public and private subnets using the VPC wizard. The VPC has CIDR 20.0.0.0/16. The public subnet uses CIDR 20.0.1.0/24. The user is planning to host a web server in the public subnet (port 80) and a DB server in the private subnet (port 3306). The user is configuring a security group for the public subnet (WebSecGrp) and the private subnet (DBSecGrp). Which of the below mentioned entries is required in the web server security group (WebSecGrp)?
- Configure Destination as DB Security group ID (DbSecGrp) for port 3306 Outbound
- Configure port 80 for Destination 0.0.0.0/0 Outbound
- Configure port 3306 for source 20.0.0.0/24 InBound
- Configure port 80 InBound for source 20.0.0.0/16
- A user has created a VPC with CIDR 20.0.0.0/16. The user has created one subnet with CIDR 20.0.0.0/16 by mistake. The user is trying to create another subnet of CIDR 20.0.0.1/24. How can the user create the second subnet?
- There is no need to update the subnet as VPC automatically adjusts the CIDR of the first subnet based on the second subnet’s CIDR
- The user can modify the first subnet CIDR from the console
- It is not possible to create a second subnet as one subnet with the same CIDR as the VPC has been created
- The user can modify the first subnet CIDR with AWS CLI
- A user has setup a VPC with CIDR 20.0.0.0/16. The VPC has a private subnet (20.0.1.0/24) and a public subnet (20.0.0.0/24). The user’s data centre has CIDR of 20.0.54.0/24 and 20.1.0.0/24. If the private subnet wants to communicate with the data centre, what will happen?
- It will allow traffic communication on both the CIDRs of the data centre
- It will not allow traffic with data centre on CIDR 20.1.0.0/24 but allows traffic communication on 20.0.54.0/24
- It will not allow traffic communication on any of the data centre CIDRs
- It will allow traffic with data centre on CIDR 20.1.0.0/24 but does not allow on 20.0.54.0/24 (as the CIDR block would be overlapping)
- A user has created a VPC with public and private subnets using the VPC wizard. The VPC has CIDR 20.0.0.0/16. The private subnet uses CIDR 20.0.0.0/24 . The NAT instance ID is i-a12345. Which of the below mentioned entries are required in the main route table attached with the private subnet to allow instances to connect with the internet?
- Destination: 0.0.0.0/0 and Target: i-a12345
- Destination: 20.0.0.0/0 and Target: 80
- Destination: 20.0.0.0/0 and Target: i-a12345
- Destination: 20.0.0.0/24 and Target: i-a12345
- A user has created a VPC with CIDR 20.0.0.0/16 using the wizard. The user has created a public subnet CIDR (20.0.0.0/24) and VPN only subnets CIDR (20.0.1.0/24) along with the VPN gateway (vgw-12345) to connect to the user’s data centre. The user’s data centre has CIDR 172.28.0.0/12. The user has also setup a NAT instance (i-123456) to allow traffic to the internet from the VPN subnet. Which of the below mentioned options is not a valid entry for the main route table in this scenario?
- Destination: 20.0.1.0/24 and Target: i-12345
- Destination: 0.0.0.0/0 and Target: i-12345
- Destination: 172.28.0.0/12 and Target: vgw-12345
- Destination: 20.0.0.0/16 and Target: local
- A user has created a VPC with CIDR 20.0.0.0/16. The user has created one subnet with CIDR 20.0.0.0/16 in this VPC. The user is trying to create another subnet with the same VPC for CIDR 20.0.0.1/24. What will happen in this scenario?
- The VPC will modify the first subnet CIDR automatically to allow the second subnet IP range
- It is not possible to create a subnet with the same CIDR as VPC
- The second subnet will be created
- It will throw a CIDR overlaps error
- A user has created a VPC with CIDR 20.0.0.0/16 using the wizard. The user has created both Public and VPN-Only subnets along with hardware VPN access to connect to the user’s data centre. The user has not yet launched any instance as well as modified or deleted any setup. He wants to delete this VPC from the console. Will the console allow the user to delete the VPC?
- Yes, the console will delete all the setups and also delete the virtual private gateway
- No, the console will ask the user to manually detach the virtual private gateway first and then allow deleting the VPC
- Yes, the console will delete all the setups and detach the virtual private gateway
- No, since the NAT instance is running
- A user has created a VPC with the public and private subnets using the VPC wizard. The VPC has CIDR 20.0.0.0/16. The public subnet uses CIDR 20.0.1.0/24. The user is planning to host a web server in the public subnet (port 80) and a DB server in the private subnet (port 3306). The user is configuring a security group for the public subnet (WebSecGrp) and the private subnet (DBSecGrp). Which of the below mentioned entries is required in the private subnet database security group (DBSecGrp)?
- Allow Inbound on port 3306 for Source Web Server Security Group (WebSecGrp)
- Allow Inbound on port 3306 from source 20.0.0.0/16
- Allow Outbound on port 3306 for Destination Web Server Security Group (WebSecGrp.
- Allow Outbound on port 80 for Destination NAT Instance IP
- A user has created a VPC with a subnet and a security group. The user has launched an instance in that subnet and attached a public IP. The user is still unable to connect to the instance. The internet gateway has also been created. What can be the reason for the error?
- The internet gateway is not configured with the route table
- The private IP is not present
- The outbound traffic on the security group is disabled
- The internet gateway is not configured with the security group
- A user has created a subnet in VPC and launched an EC2 instance within it. The user has not selected the option to assign the IP address while launching the instance. Which of the below mentioned statements is true with respect to the Instance requiring access to the Internet?
- The instance will always have a public DNS attached to the instance by default
- The user can directly attach an elastic IP to the instance
- The instance will never launch if the public IP is not assigned
- The user would need to create an internet gateway and then attach an elastic IP to the instance to connect from internet
- A user has created a VPC with public and private subnets using the VPC wizard. Which of the below mentioned statements is not true in this scenario?
- VPC will create a routing instance and attach it with a public subnet
- VPC will create two subnets
- VPC will create one internet gateway and attach it to VPC
- VPC will launch one NAT instance with an elastic IP
- A user has created a VPC with the public subnet. The user has created a security group for that VPC. Which of the below mentioned statements is true when a security group is created?
- It can connect to the AWS services, such as S3 and RDS by default
- It will have all the inbound traffic by default
- It will have all the outbound traffic by default
- It will by default allow traffic to the internet gateway
- A user has created a VPC with CIDR 20.0.0.0/16 using VPC Wizard. The user has created a public CIDR (20.0.0.0/24) and a VPN only subnet CIDR (20.0.1.0/24) along with the hardware VPN access to connect to the user’s data centre. Which of the below mentioned components is not present when the VPC is setup with the wizard?
- Main route table attached with a VPN only subnet
- A NAT instance configured to allow the VPN subnet instances to connect with the internet
- Custom route table attached with a public subnet
- An internet gateway for a public subnet
- A user has created a VPC with public and private subnets using the VPC wizard. The user has not launched any instance manually and is trying to delete the VPC. What will happen in this scenario?
- It will not allow to delete the VPC as it has subnets with route tables
- It will not allow to delete the VPC since it has a running route instance
- It will terminate the VPC along with all the instances launched by the wizard
- It will not allow to delete the VPC since it has a running NAT instance
- A user has created a public subnet with VPC and launched an EC2 instance within it. The user is trying to delete the subnet. What will happen in this scenario?
- It will delete the subnet and make the EC2 instance as a part of the default subnet
- It will not allow the user to delete the subnet until the instances are terminated
- It will delete the subnet as well as terminate the instances
- Subnet can never be deleted independently, but the user has to delete the VPC first
- A user has created a VPC with CIDR 20.0.0.0/24. The user has created a public subnet with CIDR 20.0.0.0/25 and a private subnet with CIDR 20.0.0.128/25. The user has launched one instance each in the private and public subnets. Which of the below mentioned options cannot be the correct IP address (private IP) assigned to an instance in the public or private subnet?
- 20.0.0.255
- 20.0.0.132
- 20.0.0.122
- 20.0.0.55
- A user has created a VPC with CIDR 20.0.0.0/16. The user has created public and VPN only subnets along with hardware VPN access to connect to the user’s datacenter. The user wants to make so that all traffic coming to the public subnet follows the organization’s proxy policy. How can the user make this happen?
- Setting up a NAT with the proxy protocol and configure that the public subnet receives traffic from NAT
- Setting up a proxy policy in the internet gateway connected with the public subnet
- It is not possible to setup the proxy policy for a public subnet
- Setting the route table and security group of the public subnet which receives traffic from a virtual private gateway
- A user has created a VPC with CIDR 20.0.0.0/16 using the wizard. The user has created a public subnet CIDR (20.0.0.0/24) and VPN only subnets CIDR (20.0.1.0/24) along with the VPN gateway (vgw-12345) to connect to the user’s data centre. Which of the below mentioned options is a valid entry for the main route table in this scenario?
- Destination: 20.0.0.0/24 and Target: vgw-12345
- Destination: 20.0.0.0/16 and Target: ALL
- Destination: 20.0.1.0/16 and Target: vgw-12345
- Destination: 0.0.0.0/0 and Target: vgw-12345
- Which two components provide connectivity with external networks? When attached to an Amazon VPC which two components provide connectivity with external networks? Choose 2 answers
- Elastic IPs (EIP) (Does not provide connectivity, public IP address will do as well)
- NAT Gateway (NAT) (Not Attached to VPC and still needs IGW)
- Internet Gateway (IGW)
- Virtual Private Gateway (VGW)
- You are attempting to connect to an instance in Amazon VPC without success You have already verified that the VPC has an Internet Gateway (IGW) the instance has an associated Elastic IP (EIP) and correct security group rules are in place. Which VPC component should you evaluate next?
- The configuration of a NAT instance
- The configuration of the Routing Table
- The configuration of the internet Gateway (IGW)
- The configuration of SRC/DST checking
- If you want to launch Amazon Elastic Compute Cloud (EC2) Instances and assign each Instance a predetermined private IP address you should:
- Assign a group or sequential Elastic IP address to the instances
- Launch the instances in a Placement Group
- Launch the instances in the Amazon virtual Private Cloud (VPC)
- Use standard EC2 instances since each instance gets a private Domain Name Service (DNS) already
- Launch the Instance from a private Amazon Machine image (AMI)
- A user has recently started using EC2. The user launched one EC2 instance in the default subnet in EC2-VPC Which of the below mentioned options is not attached or available with the EC2 instance when it is launched?
- Public IP address
- Internet gateway
- Elastic IP
- Private IP address
- A user has created a VPC with CIDR 20.0.0.0/24. The user has created a public subnet with CIDR 20.0.0.0/25. The user is trying to create the private subnet with CIDR 20.0.0.128/25. Which of the below mentioned statements is true in this scenario?
- It will not allow the user to create the private subnet due to a CIDR overlap
- It will allow the user to create a private subnet with CIDR as 20.0.0.128/25
- This statement is wrong as AWS does not allow CIDR 20.0.0.0/25
- It will not allow the user to create a private subnet due to a wrong CIDR range
- A user has created a VPC with CIDR 20.0.0.0/16 with only a private subnet and VPN connection using the VPC wizard. The user wants to connect to the instance in a private subnet over SSH. How should the user define the security rule for SSH?
- Allow Inbound traffic on port 22 from the user’s network
- The user has to create an instance in EC2 Classic with an elastic IP and configure the security group of a private subnet to allow SSH from that elastic IP
- The user can connect to a instance in a private subnet using the NAT instance
- Allow Inbound traffic on port 80 and 22 to allow the user to connect to a private subnet over the Internet
- A company wants to implement their website in a virtual private cloud (VPC). The web tier will use an Auto Scaling group across multiple Availability Zones (AZs). The database will use Multi-AZ RDS MySQL and should not be publicly accessible. What is the minimum number of subnets that need to be configured in the VPC?
- 1
- 2
- 3
- 4 (2 public subnets for web instances in multiple AZs and 2 private subnets for RDS Multi-AZ)
- Which of the following are characteristics of Amazon VPC subnets? Choose 2 answers
- Each subnet maps to a single Availability Zone
- A CIDR block mask of /25 is the smallest range supported
- Instances in a private subnet can communicate with the Internet only if they have an Elastic IP.
- By default, all subnets can route between each other, whether they are private or public
- Each subnet spans at least 2 Availability zones to provide a high-availability environment
- You need to design a VPC for a web-application consisting of an Elastic Load Balancer (ELB). a fleet of web/application servers, and an RDS database The entire Infrastructure must be distributed over 2 availability zones. Which VPC configuration works while assuring the database is not available from the Internet?
- One public subnet for ELB one public subnet for the web-servers, and one private subnet for the database
- One public subnet for ELB two private subnets for the web-servers, two private subnets for RDS
- Two public subnets for ELB two private subnets for the web-servers and two private subnets for RDS
- Two public subnets for ELB two public subnets for the web-servers, and two public subnets for RDS
- You have deployed a three-tier web application in a VPC with a CIDR block of 10.0.0.0/28. You initially deploy two web servers, two application servers, two database servers and one NAT instance tor a total of seven EC2 instances. The web, application and database servers are deployed across two availability zones (AZs). You also deploy an ELB in front of the two web servers, and use Route53 for DNS Web traffic gradually increases in the first few days following the deployment, so you attempt to double the number of instances in each tier of the application to handle the new load unfortunately some of these new instances fail to launch. Which of the following could the root caused? (Choose 2 answers) [PROFESSIONAL]
- The Internet Gateway (IGW) of your VPC has scaled-up adding more instances to handle the traffic spike, reducing the number of available private IP addresses for new instance launches.
- AWS reserves one IP address in each subnet’s CIDR block for Route53 so you do not have enough addresses left to launch all of the new EC2 instances.
- AWS reserves the first and the last private IP address in each subnet’s CIDR block so you do not have enough addresses left to launch all of the new EC2 instances.
- The ELB has scaled-up. Adding more instances to handle the traffic reducing the number of available private IP addresses for new instance launches
- AWS reserves the first four and the last IP address in each subnet’s CIDR block so you do not have enough addresses left to launch all of the new EC2 instances.
- A user wants to access RDS from an EC2 instance using IP addresses. Both RDS and EC2 are in the same region, but different AZs. Which of the below mentioned options help configure that the instance is accessed faster?
- Configure the Private IP of the Instance in RDS security group (Recommended as the data is transferred within the the Amazon network and not through internet – Refer link)
- Security group of EC2 allowed in the RDS security group
- Configuring the elastic IP of the instance in RDS security group
- Configure the Public IP of the instance in RDS security group
- In regards to VPC, select the correct statement:
- You can associate multiple subnets with the same Route Table.
- You can associate multiple subnets with the same Route Table, but you can’t associate a subnet with only one Route Table.
- You can’t associate multiple subnets with the same Route Table.
- None of these.
- You need to design a VPC for a web-application consisting of an ELB a fleet of web application servers, and an RDS DB. The entire infrastructure must be distributed over 2 AZ. Which VPC configuration works while assuring the DB is not available from the Internet?
- One Public Subnet for ELB, one Public Subnet for the web-servers, and one private subnet for the DB
- One Public Subnet for ELB, two Private Subnets for the web-servers, and two private subnets for the RDS
- Two Public Subnets for ELB, two private Subnet for the web-servers, and two private subnet for the RDS
- Two Public Subnets for ELB, two Public Subnet for the web-servers, and two public subnets for the RDS
- You have an Amazon VPC with one private subnet and one public subnet with a Network Address Translator (NAT) server. You are creating a group of Amazon Elastic Cloud Compute (EC2) instances that configure themselves at startup via downloading a bootstrapping script from Amazon Simple Storage Service (S3) that deploys an application via GIT. Which setup provides the highest level of security?
- Amazon EC2 instances in private subnet, no EIPs, route outgoing traffic via the NAT
- Amazon EC2 instances in public subnet, no EIPs, route outgoing traffic via the Internet Gateway (IGW)
- Amazon EC2 instances in private subnet, assign EIPs, route outgoing traffic via the Internet Gateway (IGW)
- Amazon EC2 instances in public subnet, assign EIPs, route outgoing traffic via the NAT
- You have launched an Amazon Elastic Compute Cloud (EC2) instance into a public subnet with a primary private IP address assigned, an internet gateway is attached to the VPC, and the public route table is configured to send all Internet-based traffic to the Internet gateway. The instance security group is set to allow all outbound traffic but cannot access the Internet. Why is the Internet unreachable from this instance?
- The instance does not have a public IP address
- The Internet gateway security group must allow all outbound traffic.
- The instance security group must allow all inbound traffic.
- The instance “Source/Destination check” property must be enabled.
- You have an environment that consists of a public subnet using Amazon VPC and 3 instances that are running in this subnet. These three instances can successfully communicate with other hosts on the Internet. You launch a fourth instance in the same subnet, using the same AMI and security group configuration you used for the others, but find that this instance cannot be accessed from the internet. What should you do to enable Internet access?
- Deploy a NAT instance into the public subnet.
- Assign an Elastic IP address to the fourth instance
- Configure a publically routable IP Address in the host OS of the fourth instance.
- Modify the routing table for the public subnet.
- You have a load balancer configured for VPC, and all back-end Amazon EC2 instances are in service. However, your web browser times out when connecting to the load balancer’s DNS name. Which options are probable causes of this behavior? Choose 2 answers
- The load balancer was not configured to use a public subnet with an Internet gateway configured
- The Amazon EC2 instances do not have a dynamically allocated private IP address
- The security groups or network ACLs are not property configured for web traffic.
- The load balancer is not configured in a private subnet with a NAT instance.
- The VPC does not have a VGW configured.
- When will you incur costs with an Elastic IP address (EIP)?
- When an EIP is allocated.
- When it is allocated and associated with a running instance.
- When it is allocated and associated with a stopped instance.
- Costs are incurred regardless of whether the EIP is associated with a running instance.
- A company currently has a VPC with EC2 Instances. A new instance being launched, which will host an application that works on IPv6. You need to ensure that this instance can initiate outgoing traffic to the Internet. At the same time, you need to ensure that no incoming connection can be initiated from the Internet on to the instance. Which of the following would you add to the VPC for this requirement?
- A NAT Instance
- A NAT Gateway
- An Internet Gateway
- An egress-only Internet gateway