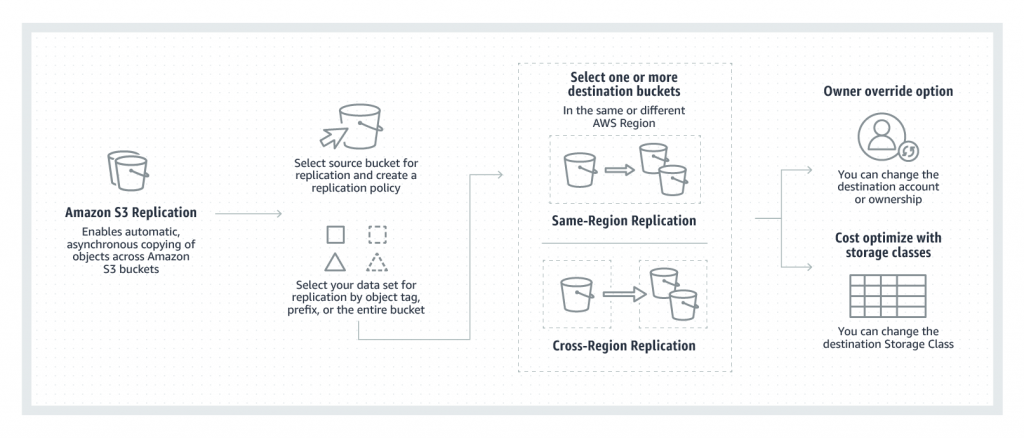
Amazon S3 Replication
- S3 Replication enables automatic, asynchronous copying of objects across S3 buckets in the same or different AWS regions.
- S3 Cross-Region Replication – CRR is used to copy objects across S3 buckets in different AWS Regions.
- S3 Same-Region Replication – SRR is used to copy objects across S3 buckets in the same AWS Regions.
- S3 Replication helps to
- Replicate objects while retaining metadata
- Replicate objects into different storage classes
- Maintain object copies under different ownership
- Keep objects stored over multiple AWS Regions
- Replicate objects within 15 minutes
- S3 can replicate all or a subset of objects with specific key name prefixes
- S3 encrypts all data in transit across AWS regions using SSL
- Object replicas in the destination bucket are exact replicas of the objects in the source bucket with the same key names and the same metadata.
- Objects may be replicated to a single destination bucket or multiple destination buckets.
- Cross-Region Replication can be useful for the following scenarios:-
- Compliance requirement to have data backed up across regions
- Minimize latency to allow users across geography to access objects
- Operational reasons compute clusters in two different regions that analyze the same set of objects
- Same-Region Replication can be useful for the following scenarios:-
- Aggregate logs into a single bucket
- Configure live replication between production and test accounts
- Abide by data sovereignty laws to store multiple copies
S3 Replication Requirements
- source and destination buckets must be versioning-enabled
- for CRR, the source and destination buckets must be in different AWS regions.
- S3 must have permission to replicate objects from that source bucket to the destination bucket on your behalf.
- If the source bucket owner also owns the object, the bucket owner has full permission to replicate the object. If not, the source bucket owner must have permission for the S3 actions
s3:GetObjectVersionands3:GetObjectVersionACLto read the object and object ACL - Setting up cross-region replication in a cross-account scenario (where the source and destination buckets are owned by different AWS accounts), the source bucket owner must have permission to replicate objects in the destination bucket.
- if the source bucket has S3 Object Lock enabled, the destination buckets must also have S3 Object Lock enabled.
- destination buckets cannot be configured as Requester Pays buckets
S3 Replication – Replicated & Not Replicated
- Only new objects created after you add a replication configuration are replicated. S3 does NOT retroactively replicate objects that existed before you added replication configuration.
- Objects encrypted using customer provided keys (SSE-C), objects encrypted at rest under an S3 managed key (SSE-S3) or a KMS key stored in AWS Key Management Service (SSE-KMS).
- S3 replicates only objects in the source bucket for which the bucket owner has permission to read objects and read ACLs
- Any object ACL updates are replicated, although there can be some delay before S3 can bring the two in sync. This applies only to objects created after you add a replication configuration to the bucket.
- S3 does NOT replicate objects in the source bucket for which the bucket owner does not have permission.
- Updates to bucket-level S3 subresources are NOT replicated, allowing different bucket configurations on the source and destination buckets
- Only customer actions are replicated & actions performed by lifecycle configuration are NOT replicated
- Replication chaining is NOT allowed, Objects in the source bucket that are replicas, created by another replication, are NOT replicated.
- S3 does NOT replicate the delete marker by default. However, you can add delete marker replication to non-tag-based rules to override it.
- S3 does NOT replicate deletion by object version ID. This protects data from malicious deletions.
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.