Google Cloud Identity
- Cloud Identity is an Identity as a Service (IDaaS) solution that helps centrally manage the users and groups.
- can be configured to federate identities between Google and other identity providers, such as Active Directory and Azure Active Directory
- also gives more control over the accounts that are used in the organization.
- Cloud Identity account is created for each of your users and groups and IAM can be used to manage access to Google Cloud resources for each Cloud Identity account.
Google Cloud Identity Management
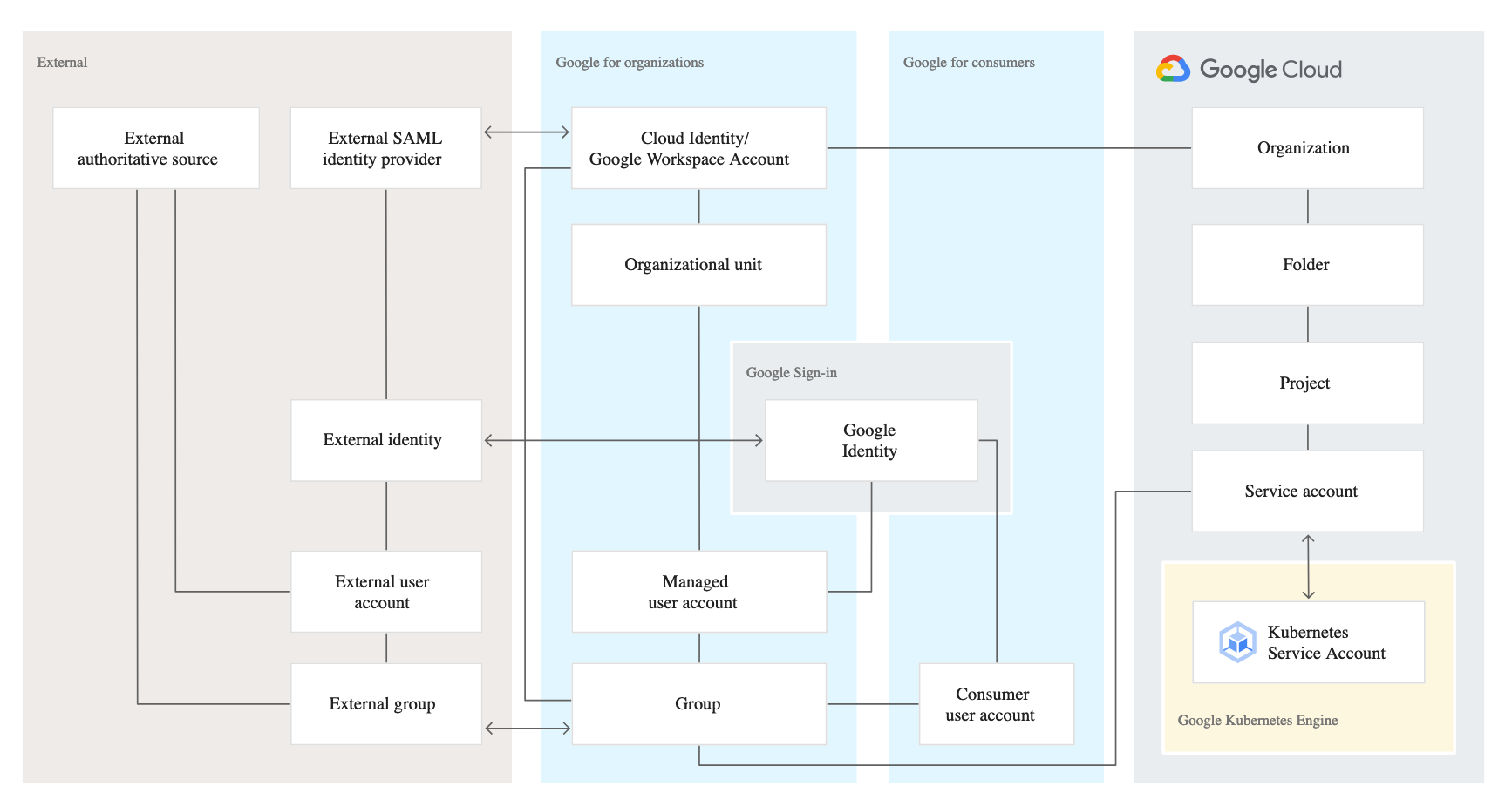
- Google identity is related to a number of other entities that are all relevant in the context of managing identities:
- Google for consumers contains the entities that are relevant for consumer-focused usage of Google services such as Gmail.
- Google for organizations contains entities managed by Cloud Identity or Google Workspace. These entities are the most relevant for managing corporate identities.
- Google Cloud contains entities that are specific to Google Cloud.
- External contains entities that are relevant if you integrate Google with an external Identity Provider (IdP).
- A Cloud Identity or Google Workspace (G Suite) account is the top-level container for users, groups, configuration, and data.
- A Cloud Identity or Google Workspace account is created when a company signs up for Cloud Identity or Google Workspace and corresponds to the notion of a tenant.
- Cloud Identity or Google Workspace account federation with an external IdP enables employees to use their existing identity and credentials to sign in to Google services.
- External IdP is the source of truth and the sole system for authentication and provides a SSO experience for the employees across applications
- With single sign-on enabled, Cloud Identity or Google Workspace relays authentication decisions to the SAML IdP.
- In SAML terms, Cloud Identity or Google Workspace acts as a service provider that trusts the SAML IdP to verify a user’s identity on its behalf.
- Each Cloud Identity or Google Workspace account can refer to at most one external IdP
Single Sign-on – SSO
- Cloud Identity or Google Workspace account can be configured to use a single sign-on (SSO).
- With SSO enabled, users are redirected to an external identity provider (IdP) for authentication.
- Using SSO can provide several advantages:
- better experience for users because they can use their existing credentials to authenticate and don’t have to enter credentials as often.
- existing IdP remains the system of record for authenticating users.
- don’t need to synchronize passwords to Cloud Identity or Google Workspace
- Cloud Identity and Google Workspace support Security Assertion Markup Language (SAML) 2.0 for single sign-on.
- SAML is an open standard for exchanging authentication and authorization data between a SAML IdP and SAML service providers.
- With SSO for Cloud Identity or Google Workspace, the external IdP is the SAML IdP and Google is the SAML service provider.
- Google implements SAML 2.0 HTTP Redirect binding.
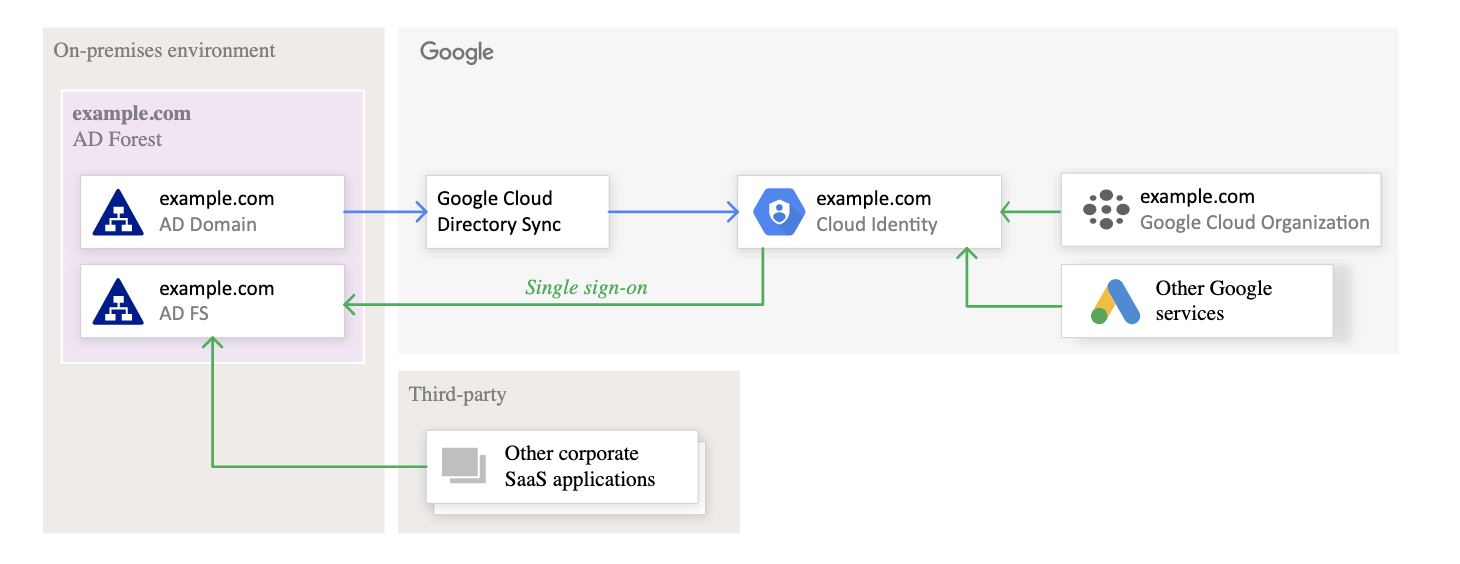
Federating Google Cloud with Active Directory
- Federating user identities between Google Cloud and existing identity management systems helps automate the maintenance of Google identities and tie their lifecycle to existing users in Active Directory.
- Federation can be supported using the following tools
- Google Cloud Directory Sync – GCDS
- is a free Google-provided tool that implements the synchronization process from Active Directory or LDAP server to Google Domain
- communicates with Google Cloud over Secure Sockets Layer (SSL) and usually runs in the existing computing environment.
- Active Directory Federation Services (AD FS)
- is provided by Microsoft as part of Windows Server.
- helps use Active Directory for federated authentication.
- runs within the existing computing environment.
- Google Cloud Directory Sync – GCDS
GCP Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- GCP services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- GCP exam questions are not updated to keep up the pace with GCP updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- Your organization has user identities in Active Directory. Your organization wants to use Active Directory as its source of truth for identities. Your organization wants to have full control over the Google accounts used by employees for all Google services, including your Google Cloud Platform (GCP) organization. What should you do?
- Use Google Cloud Directory Sync (GCDS) to synchronize users into Cloud Identity.
- Use the Cloud Identity APIs and write a script to synchronize users to Cloud Identity.
- Export users from Active Directory as a CSV and import them to Cloud Identity via the Admin Console.
- Ask each employee to create a Google account using self signup. Require that each employee use their company email address and password.
- Your company has a single sign-on (SSO) identity provider that supports Security Assertion Markup Language (SAML) integration with service providers. Your company has users in Cloud Identity. You would like users to authenticate using your company’s SSO provider. What should you do?
- In Cloud Identity, set up SSO with Google as an identity provider to access custom SAML apps.
- In Cloud Identity, set up SSO with a third-party identity provider with Google as a service provider.
- Obtain OAuth 2.0 credentials, configure the user consent screen, and set up OAuth 2.0 for Mobile & Desktop Apps.
- Obtain OAuth 2.0 credentials, configure the user consent screen, and set up OAuth 2.0 for Web Server Applications.