AWS VPC Endpoints
- VPC Endpoints enable the creation of a private connection between VPC to supported AWS services and VPC endpoint services powered by PrivateLink using its private IP address
- Endpoints do not require a public IP address, access over the Internet, NAT device, a VPN connection, or AWS Direct Connect.
- Traffic between VPC and AWS service does not leave the Amazon network
- Endpoints are virtual devices, that are horizontally scaled, redundant, and highly available VPC components that allow communication between instances in the VPC and AWS services without imposing availability risks or bandwidth constraints on your network traffic.
- Endpoints currently do not support cross-region requests, ensure that the endpoint is created in the same region as the S3 bucket
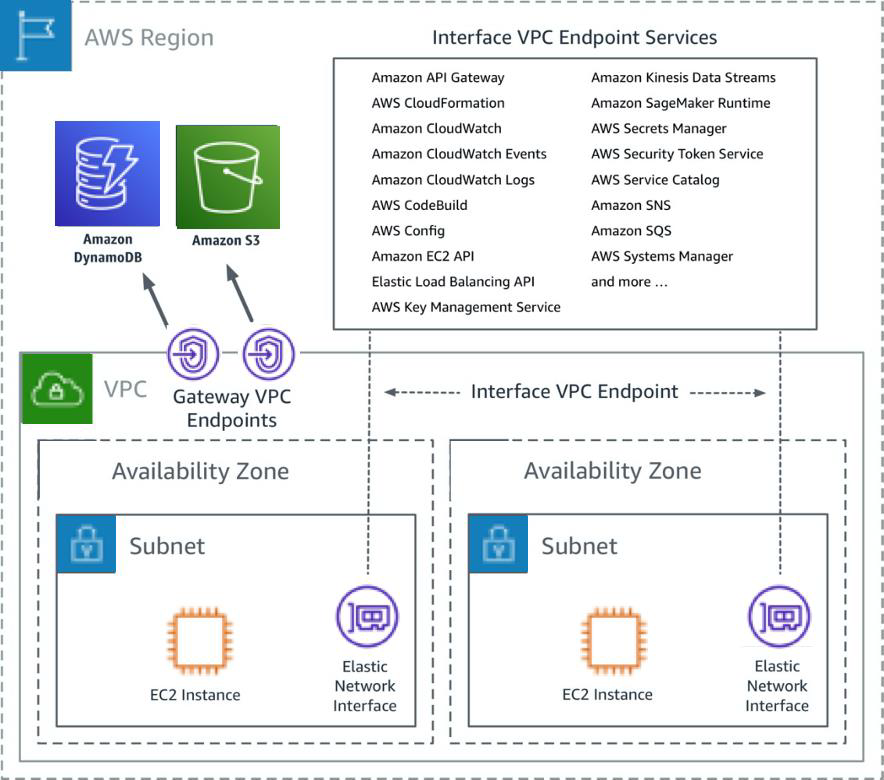
- AWS currently supports the following types of Endpoints
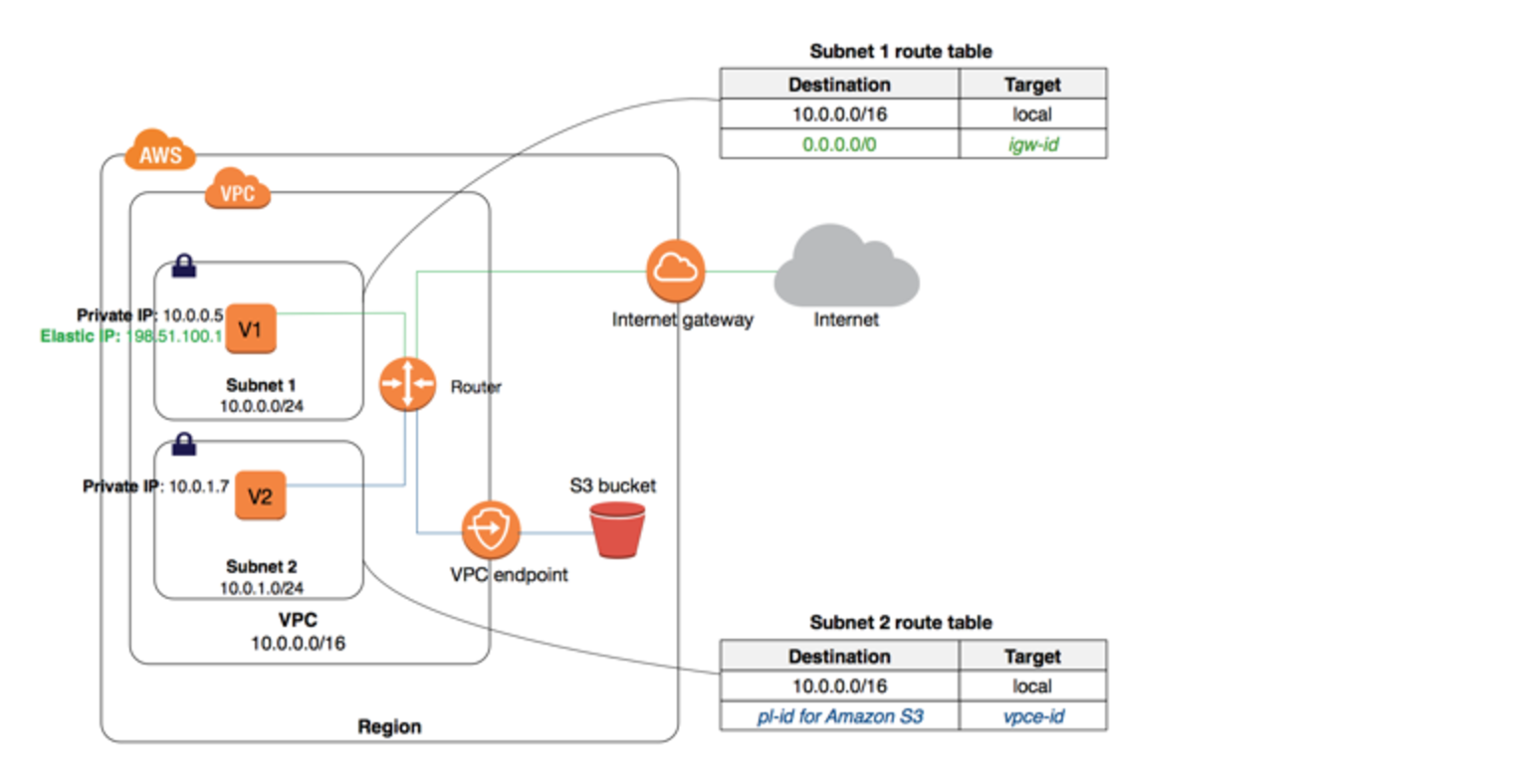
VPC Gateway Endpoints
- A VPC Gateway Endpoint is a gateway that is a target for a specified route in the route table, used for traffic destined for a supported AWS service.
- Gateway Endpoints currently supports S3 and DynamoDB services
- Gateway Endpoints do not require an Internet gateway or a NAT device for the VPC.
- Gateway endpoints do not enable AWS PrivateLink.
- VPC Endpoint policy and Resource-based policies can be used for fine-grained access control.
VPC Interface Endpoints – PrivateLink
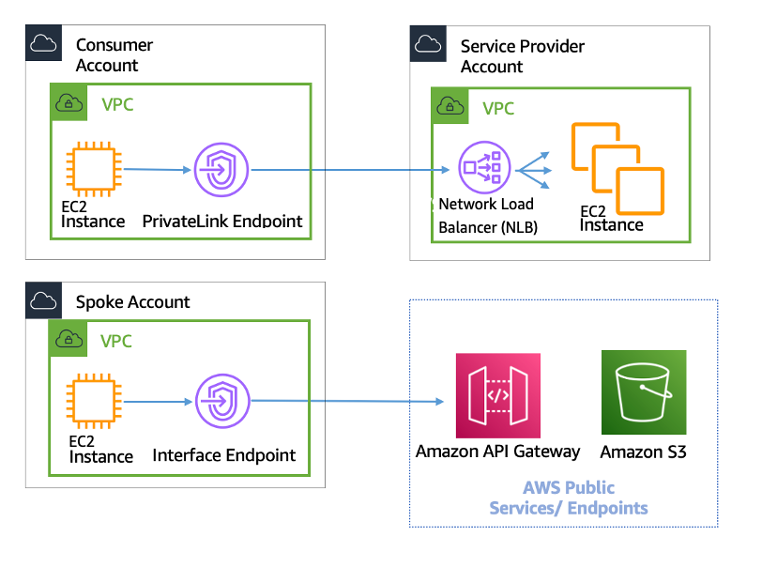
- VPC Interface endpoints enable connectivity to services powered by AWS PrivateLink.
- Services include AWS services like CloudTrail, CloudWatch, etc., services hosted by other AWS customers and partners in their own VPCs (referred to as endpoint services), and supported AWS Marketplace partner services.
- Interface Endpoints only allow traffic from VPC resources to the endpoints and not vice versa
- PrivateLink endpoints can be accessed across both intra- and inter-region VPC peering connections, Direct Connect, and VPN connections.
- VPC Interface Endpoints, by default, have an address like
vpce-svc-01234567890abcdef.us-east-1.vpce.amazonaws.comwhich needs application changes to point to the service. - Private DNS name feature allows consumers to use AWS service public default DNS names which would point to the private VPC endpoint service.
- Interface Endpoints can be used to create custom applications in VPC and configure them as an AWS PrivateLink-powered service (referred to as an endpoint service) exposed through a Network Load Balancer.
- Custom applications can be hosted within AWS or on-premises (via Direct Connect or VPN)
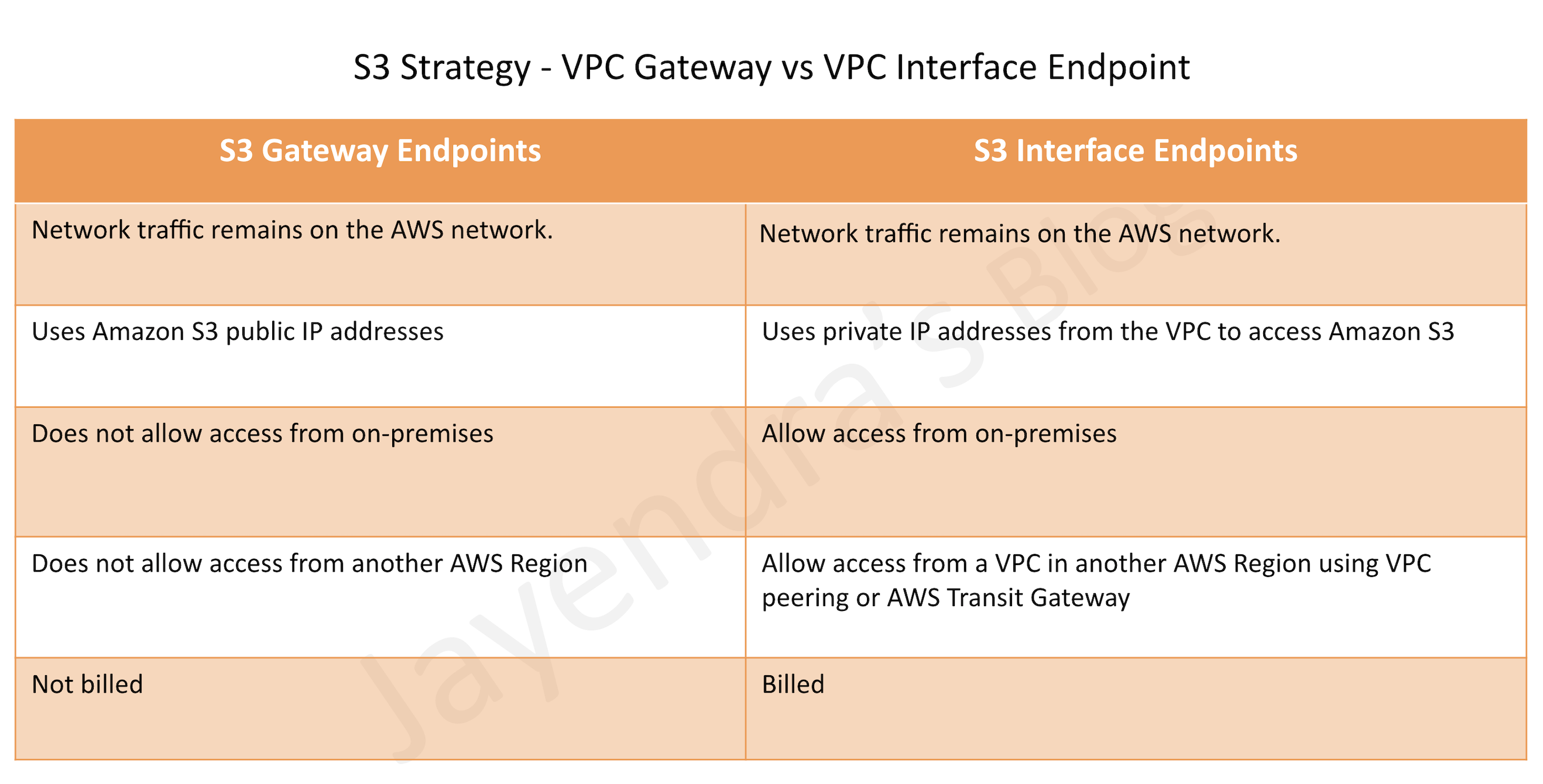
S3 VPC Endpoints Strategy
S3 is now accessible with both Gateway Endpoints and Interface Endpoints.
AWS Certification Exam Practice Questions
- Questions are collected from Internet and the answers are marked as per my knowledge and understanding (which might differ with yours).
- AWS services are updated everyday and both the answers and questions might be outdated soon, so research accordingly.
- AWS exam questions are not updated to keep up the pace with AWS updates, so even if the underlying feature has changed the question might not be updated
- Open to further feedback, discussion and correction.
- You have an application running on an Amazon EC2 instance that uploads 10 GB video objects to amazon S3. Video uploads are taking longer than expected inspite of using multipart upload cause of internet bandwidth, resulting in poor application performance. Which action can help improve the upload performance?
- Apply an Amazon S3 bucket policy
- Use Amazon EBS provisioned IOPS
- Use VPC endpoints for S3
- Request a service limit increase
- What are the services supported by VPC endpoints, using Gateway endpoint type? Choose 2 answers
- Amazon S3
- Amazon EFS
- Amazon DynamoDB
- Amazon Glacier
- Amazon SQS
- What are the different types of endpoint types supported by VPC endpoints? Choose 2 Answers
- Gateway
- Classic
- Interface
- Virtual
- Network
- An application running on EC2 instances processes sensitive information stored on Amazon S3. The information is accessed over the Internet. The security team is concerned that the Internet connectivity to Amazon S3 is a security risk. Which solution will resolve the security concern?
- Access the data through an Internet Gateway.
- Access the data through a VPN connection.
- Access the data through a NAT Gateway.
- Access the data through a VPC endpoint for Amazon S3.
- You need to design a VPC for a three-tier architecture, a web application consisting of an Elastic Load Balancer (ELB), a fleet of web/application servers, and a backend consisting of an RDS database. The entire Infrastructure must be distributed over 2 availability zones. Which VPC configuration works while assuring the least components are exposed to Internet?
- Two public subnets for ELB, two private subnets for the web-servers, two private subnets for RDS and DynamoDB
- Two public subnets for ELB and web-servers, two private subnets for RDS and DynamoDB
- Two public subnets for ELB, two private subnets for the web-servers, two private subnets for RDS and VPC Endpoints for DynamoDB
- Two public subnets for ELB and web-servers, two private subnets for RDS and VPC Endpoints for DynamoDB
AWS currently supports end points for both S3 and DynamoDB as well. Please correct it.
Thanks Pradeep seems a latest enhancement, will check and add the same.
wow quick response. thank you.
AWS currently supports endpoints for S3 service only
>New update: DynamoDB
Thanks doanda86, yup there has been an update from AWS sometime back. Update the same.
Jayendra, It appears the link to the document at the end is broken/outdated. It looks like this link takes you to the intended location: https://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/vpc-endpoints.html
Thanks for the good info.
thanks Dave, it seems like Amazon Affiliate script is breaking the docs link. Let me check further.
Jayendra , Request you to kindly help how can i prepare for AWS interview
Hi Puneet, for interviews I usually recommend get your theory concepts right. Get your hands on using Free Tier, Qwiklabs, and Implement AWS projects. Also watch Re-Invent videos on architecture mainly.
We have our application on Singapore Region and want to use the SES Service (Closest Endpoint) in EU-Ireland.Apparently VPC Endpoint doesn’t supports Service in cross region. PrivateLink doesn’t look promising (no clarity whether it supports cross region AWS Service (SES) if though how the connectivity can be established between regions,using Direct Connect or VPN ? Any idea how this can be achieved
Why not try an alternative for SES as a SaaS service instead ?
Hi Jayendra,
Great blog. Always helped me in clearing the certifications.
Noticed that we can tag the VPC endpoint now (https://docs.aws.amazon.com/vpc/latest/userguide/vpce-interface.html). Please update it.
Thanks Surupa, will add the same.
For Question 5, how come (a) also is not correct. Aren’t the same number of servers exposed to internet in both (a) and (d). The only difference is that in (d) we using Endpoint
The question is asking for least number of components exposed to internet. In both answers it is the 2 web servers.
If you can please clarify why (d) picked over (a).
Thanks in advance. Fantastic Blog!
for Q5, B & D have web servers in public subnet and hence exposed. Between a and c, you don’t have DynamoDB in private subnet and you can limit you applications access to DynamoDB using VPC endpoint which is internal and does not go through internet
Hi,
Answer a) in question 5: “(…) two private subnets for RDS and DynamoDB”. I read it as those two private subnets are for both: RDS and DynamoDB. Therefore answers a) and c) would result in the same? Or am I missing something?
Really nice job with this blog.
DynamoDB does not need any subnets, so A and C are still different options with C being more correct.
Hi Jayendra
Great Informative article. I have question about cross account capability for vpc endpoints. Use case I am looking for, is, I want to have private API connectivity to APIs hosted through APIGW in one account, and other ec2 instances in different accounts, but coming under same org.
Can I have a vpc endpoint enabling private connectivity between vpc in Account A, to a service (APIGW) in Account B. Or what would be the typical approach here. It would be great to know your thoughts on this.
You can expose the API as private Link @ https://docs.aws.amazon.com/vpc/latest/userguide/endpoint-service.html.
Hi Jayendra,
Nice article. One thing that is not clear, consider the following scenario:
Lets say I have a ECS service and a lambda running in a VPC. Both ECS service and lambda access SQS service and Postgres database in RDS. Everythings works. Now, I create a VPC endpoint for SQS. Do I need another VPC endpoint for my services to access RDS? I know the RDS traffic leaves the VPC but my question is will the services be able to access RDS as before?
RDS does not need VPC endpoint. As Lambda is already in VPC, it can access RDS private endpoint directly.
Hi sir pls answer,
A sysops administrator created an AWS Lambda function within a VPC with no access to the Internet. The Lambda function pulls messages from an Amazon SQS queue and stores them in an Amazon RDS instance in the same VPC. After executing the Lambda function, the data is not showing up on the RDS instance.Which of the following are possible causes for this? (Choose two.)
* A. A VPC endpoint has not been created for Amazon RDS
* B. A VPC endpoint has not been created for Amazon SQS
* C. The RDS security group is not allowing connections from the Lambda function
* D. The subnet associated with the Lambda function does not have an internet gateway attached
* E. The subnet associated with the Lambda function has a NAT gateway.
B & C. SQS needs VPC Interface Endpoint and RDS should allow connections from Lambda.
Q5 bothers me much – the correct answer has VPC Endpoint for DynamoDB, which is surely meeting the requirements of least traffic outside AWS.
BUT… The question doesn’t ask for DynamoDB at all… Neither it does for S3 nor for any other AWS service that would need to use VPC Endpoint.
The answer C is still the only correct answer, but it doesn’t really fit to the question.
It’s just a valid option from the available options.
Endpoint connections cannot be extended out of a VPC i.e. resources across the VPN connection, VPC peering connection, AWS Direct Connect connection cannot use the endpoint
Is not correct as from Oct 10, 2018
AWS PrivateLink now supports access over Inter-Region VPC Peering
Its still a valid limitation for VPC Gateway endpoints.